Strategic Vigilance: Advancing Early Detection Through Risk-Based Surveillance
This article provides a comprehensive analysis of risk-based surveillance strategies for the early detection of threats in biomedical and clinical research.
Strategic Vigilance: Advancing Early Detection Through Risk-Based Surveillance
Abstract
This article provides a comprehensive analysis of risk-based surveillance strategies for the early detection of threats in biomedical and clinical research. Tailored for researchers, scientists, and drug development professionals, it explores the foundational principles and ethical imperatives of risk-based monitoring, details innovative methodological applications from drug safety to infectious diseases, addresses critical implementation challenges in diverse settings, and presents rigorous validation frameworks. By synthesizing insights from clinical development, public health, and regulatory science, this review serves as a strategic guide for enhancing the sensitivity, efficiency, and global harmonization of early warning systems.
The Bedrock of Vigilance: Principles and Imperatives of Risk-Based Surveillance
The journey from the Hippocratic Oath to modern International Council for Harmonisation (ICH) guidelines represents a profound evolution in medical ethics and regulatory science. This transition reflects a shift from individual physician virtue to systematically implemented, risk-proportioned oversight frameworks that protect patients and ensure data integrity across global clinical research. The Hippocratic Oath, formulated around 400 BC, established the fundamental ethical principle of beneficence—to "do no harm or injustice" to patients [1] [2]. For centuries, this oath served as the primary ethical compass for physicians, emphasizing patient confidentiality, gratitude to teachers, and the sanctity of the patient-physician relationship [1].
In contemporary medicine, these foundational principles have been systematically codified into regulatory frameworks that govern clinical research worldwide. The ICH Good Clinical Practice (GCP) guidelines, particularly the upcoming E6(R3) revision scheduled for implementation in 2025, represent the modern embodiment of these ethical commitments [3] [4]. This evolution addresses complex challenges in global drug development, digital health technologies, and risk-based surveillance strategies that were unimaginable in Hippocrates' era. The progression from personal ethical commitment to structured regulatory oversight demonstrates how medicine has maintained its ethical foundations while adapting to enormous scientific and societal changes.
Historical Foundations: From Hippocratic Oath to Modern Bioethics
Core Principles of the Hippocratic Oath
The Hippocratic Oath established several enduring ethical principles that continue to resonate in modern medical practice. Its directives include confidentiality ("Whatever I see or hear in the lives of my patients... I will keep secret"), beneficence ("I will use treatment to help the sick according to my ability and judgment"), and non-maleficence ("I will do no harm or injustice to them") [1] [2]. The oath also emphasized respect for teachers and the sharing of medical knowledge, establishing a culture of mentorship and continuous learning within the profession. These principles formed the ethical bedrock of medicine for centuries, creating a foundation of trust between physicians and patients.
Limitations in Modern Contexts
Despite its enduring values, the original Hippocratic Oath faces significant limitations in contemporary medical practice. The oath was created for a paternalistic model of medicine where physicians made decisions with minimal patient input, failing to address modern concepts of patient autonomy and informed consent [1]. Its prohibitions against abortion and euthanasia conflict with legal medical practices in many jurisdictions, where abortion is legal under specific conditions and euthanasia or physician-assisted dying is permitted in several countries [1]. The oath's exclusion of women from medical practice (it was originally intended for male physicians only) and its swearing to Greek gods make it culturally problematic in today's multicultural, pluralistic societies [1] [5]. Furthermore, it provides no guidance on contemporary challenges such as digital health technologies, health insurance systems, corporate influences on medicine, or legal liabilities that modern physicians navigate regularly [1].
Key Historical Developments in Research Ethics
The 20th century witnessed crucial developments that exposed the limitations of relying solely on individual physician ethics and catalyzed the creation of systematic research regulations. The Nuremberg Code (1947) established the fundamental requirement of voluntary informed consent following the atrocities of Nazi medical experiments [6]. The Declaration of Helsinki (1964) further developed principles for human research ethics, emphasizing subject welfare and risk-benefit assessment [6]. The Belmont Report (1979) articulated three core ethical principles: respect for persons, justice, and beneficence, providing the foundation for modern institutional review boards (IRBs) [6]. These developments reflected growing recognition that individual ethical commitments, while necessary, required supplementation with structured oversight systems to protect vulnerable populations in increasingly complex research environments.
Table 1: Historical Evolution of Medical Ethics and Regulations
| Time Period | Key Document/Event | Core Ethical Principles | Regulatory Impact |
|---|---|---|---|
| 400 BC | Hippocratic Oath | Beneficence, Confidentiality, Non-maleficence | Individual physician commitment |
| 1947 | Nuremberg Code | Voluntary consent, Avoid unnecessary suffering | Foundation for research ethics |
| 1964 | Declaration of Helsinki | Risk-benefit assessment, Subject welfare | International research standards |
| 1979 | Belmont Report | Respect for persons, Justice, Beneficence | IRB requirements |
| 1996 | ICH E6(R1) GCP | Data quality, Subject protection | Harmonized global clinical trials |
| 2016 | ICH E6(R2) GCP | Risk-based monitoring, Quality management | Enhanced oversight efficiency |
| 2025 (anticipated) | ICH E6(R3) GCP | Proportionality, Digital trials, Data governance | Modernized for current research landscape |
The Rise of Risk-Based Approaches in Surveillance and Monitoring
Fundamental Principles of Risk-Based Surveillance
Risk-based surveillance represents a strategic methodology that directs monitoring resources toward the most critical elements that impact patient safety and data quality. This approach acknowledges that not all processes, data, or sites carry equal risk in clinical research or disease surveillance. The fundamental principle involves identifying critical-to-quality factors that are essential to trial integrity and participant safety, then allocating monitoring resources proportionately to these risks [3] [7]. This represents a significant shift from traditional "one-size-fits-all" monitoring approaches toward targeted, efficient oversight that enhances detection capabilities while optimizing resource utilization.
Risk-based methodologies have demonstrated particular value in early detection systems for emerging threats. In plant pathology, sophisticated risk-based surveillance optimization has shown that concentrating solely on the highest-risk sites may be suboptimal; instead, strategically distributing resources across multiple locations accounting for spatial correlations in risk can significantly improve detection probability [8] [9]. This "don't put all your eggs in one basket" approach has relevance for clinical trial monitoring, where diversifying surveillance strategies may provide more robust safety detection than focusing exclusively on presumed highest-risk sites.
Application in Clinical Trial Monitoring
The implementation of risk-based monitoring (RBM) in clinical trials represents a practical application of these surveillance principles. RBM employs centralized monitoring activities complemented by targeted on-site monitoring focused on critical data and processes [10] [7]. This approach utilizes key risk indicators (KRIs) and quality tolerance limits (QTLs) to identify sites or processes deviating from expected patterns, enabling proactive intervention before issues impact patient safety or data integrity [3]. The U.S. Food and Drug Administration (FDA) has explicitly endorsed this approach through its guidance on "Oversight of Clinical Investigations—A Risk-Based Approach to Monitoring," emphasizing that sponsors should focus monitoring activities on the most important aspects of study conduct and reporting [10].
The advantages of risk-based monitoring are substantial. Studies have demonstrated that RBM can reduce monitoring costs by 15-30% while simultaneously improving data quality and patient safety oversight [7]. This efficiency gain comes from eliminating redundant source document verification, focusing on-site visits on higher-risk activities, and leveraging centralized statistical surveillance to identify anomalous patterns across sites. Furthermore, the risk-based approach creates a systematic framework for prioritizing monitoring activities based on their potential impact on human subject protection and trial conclusions, moving beyond tradition-based monitoring schedules toward scientifically justified oversight strategies.
Implementation Framework for Risk-Based Surveillance
Implementing an effective risk-based surveillance system requires a structured approach. The process begins with risk identification—systematically assessing all trial processes to determine which elements are most critical to patient safety and data reliability. This is followed by risk evaluation—assessing the likelihood and impact of potential errors or safety issues. Based on this evaluation, organizations develop mitigation strategies including tailored monitoring plans, targeted training, and specialized procedures for high-risk activities. Finally, continuous risk review ensures the surveillance strategy evolves as new risks emerge and existing risks change throughout the trial lifecycle [10] [3].
Table 2: Core Components of Risk-Based Surveillance Systems
| Component | Description | Application in Clinical Research | Application in Pathogen Surveillance |
|---|---|---|---|
| Risk Assessment | Systematic identification and evaluation of risks | Identify critical data points, vulnerable populations | Identify high-risk introduction pathways, susceptible hosts |
| Resource Allocation | Direction of surveillance resources based on risk | Increased monitoring at sites with protocol deviations | Enhanced sampling in areas with high introduction probability |
| Detection Methodologies | Sensitivity-specificity optimization | Statistical surveillance, centralized monitoring | Diagnostic tools with appropriate sensitivity for early detection |
| Adaptive Strategy | Evolution based on emerging data | Protocol amendments, monitoring plan updates | Surveillance strategy refinement as epidemiological understanding improves |
| Quality Indicators | Metrics to evaluate surveillance effectiveness | Quality tolerance limits, key risk indicators | Detection probability, time to detection, false positive rates |
ICH E6(R3): The Modern Implementation of Ethical Principles
Key Updates and Structural Changes
ICH E6(R3), scheduled for implementation in July 2025, represents the most significant revision of Good Clinical Practice guidelines in nearly a decade. This update fundamentally restructures the guideline into an overarching Principles document accompanied by annexes addressing specific trial types [3]. The structural reorganization includes Annex 1 for interventional clinical trials and a planned Annex 2 for "non-traditional" trial designs such as decentralized, adaptive, and platform trials [3] [4]. This modular approach provides a more flexible framework that can adapt to evolving methodological innovations while maintaining core ethical principles.
A central theme of E6(R3) is the embrace of media-neutral language that facilitates the integration of digital health technologies into clinical research [3]. The guidelines explicitly recognize electronic informed consent (eConsent), wearable devices, telemedicine visits, and electronic source documentation (eSource) as valid components of clinical trials. This modernization acknowledges the technological transformation of clinical research while maintaining rigorous standards for data quality and participant protection. By removing media-specific requirements, the guidelines encourage innovation while focusing on functional outcomes—ensuring that regardless of the technology used, the rights, safety, and well-being of trial participants remain protected.
Enhanced Ethical Protections in E6(R3)
ICH E6(R3) strengthens several ethical dimensions of clinical research that echo concerns first articulated in the Hippocratic Oath. The guideline introduces richer informed consent requirements, specifically mandating that participants receive information about data handling after withdrawal, results communication, storage duration, and safeguards protecting secondary data use [4]. This enhanced transparency respects participant autonomy in an era of increasingly complex data flows, addressing modern challenges to confidentiality that Hippocrates could not have imagined yet upholding his principle of protecting patient information.
The revision also elevates data governance from a technical concern to an ethical imperative. Chapter 4 of E6(R3) establishes an integrated framework encompassing audit trails, metadata integrity, access controls, and end-to-end data retention [4]. This formalizes sponsor responsibilities for data quality and security while empowering ethics committees to interrogate these controls as they relate to participant rights and welfare. The guidelines further signal an ethical shift through terminology changes, replacing "trial subject" with "trial participant" throughout the document to emphasize partnership and respect for autonomy [4]. This linguistic evolution reflects deeper ethical commitments to recognizing research participants as active collaborators rather than passive subjects.
Risk-Proportionate Implementation
A cornerstone of ICH E6(R3) is the principle of risk-proportionate oversight, which applies the risk-based surveillance approach to ethics review and trial conduct. The guideline explicitly encourages ethics committees to set continuing review frequency according to actual participant risk rather than calendar defaults [4]. This enables more efficient allocation of committee resources to higher-risk studies while reducing unnecessary administrative burdens on minimal-risk research. The risk-proportionate approach extends to monitoring strategies, documentation requirements, and safety reporting, creating a cohesive framework that scales oversight activities to match the specific risks of each trial.
The implementation of risk-proportionate oversight requires sophisticated risk assessment methodologies that can systematically evaluate and categorize studies based on their potential harms and vulnerabilities. Ethics committees must develop criteria for determining review intensity, considering factors such as intervention novelty, population vulnerability, endpoint criticality, and procedural complexity. This nuanced approach represents a maturation from standardized checklists toward context-sensitive ethical oversight that can more effectively protect participants while facilitating efficient research conduct.
Experimental Protocols for Risk-Based Surveillance Implementation
Protocol 1: Spatial Optimization for Early Detection Surveillance
Purpose: This protocol provides a methodology for optimizing surveillance site selection to maximize early detection probability for emerging threats, adapting approaches successfully used in plant disease surveillance [8] [9] to clinical safety monitoring.
Materials and Reagents:
- Geographic information system (GIS) software with spatial analysis capabilities
- Historical introduction risk data (e.g., prior safety events, protocol deviations)
- Host susceptibility landscape (e.g., patient population distribution, site capabilities)
- Pathogen spread parameters (e.g., communication patterns between sites, referral networks)
- Detection sensitivity specifications for monitoring methodologies
Methodology:
- Model Development: Create a spatially explicit stochastic model of threat introduction and spread through the research network, incorporating between-site transmission probabilities.
- Simulation Execution: Run multiple iterations (n≥10,000) simulating threat spread from random introduction points until predefined prevalence threshold is exceeded.
- Detection Modeling: Calculate detection probabilities for potential surveillance site arrangements using statistical detection models that account for sampling frequency and diagnostic sensitivity.
- Optimization Algorithm: Apply stochastic optimization (e.g., simulated annealing) to identify surveillance site arrangements that maximize detection probability before threshold prevalence.
- Validation: Compare optimized surveillance strategy performance against conventional risk-based targeting using holdout simulation data.
Implementation Considerations:
- Optimal surveillance arrangements account for spatial correlations in risk—distributing resources across multiple moderate-risk sites often outperforms concentration solely on highest-risk locations [8].
- Surveillance strategy should be dynamically updated as new risk information emerges throughout the trial lifecycle.
- The balance between surveillance sensitivity and resource constraints should be explicitly quantified to support rational resource allocation decisions.
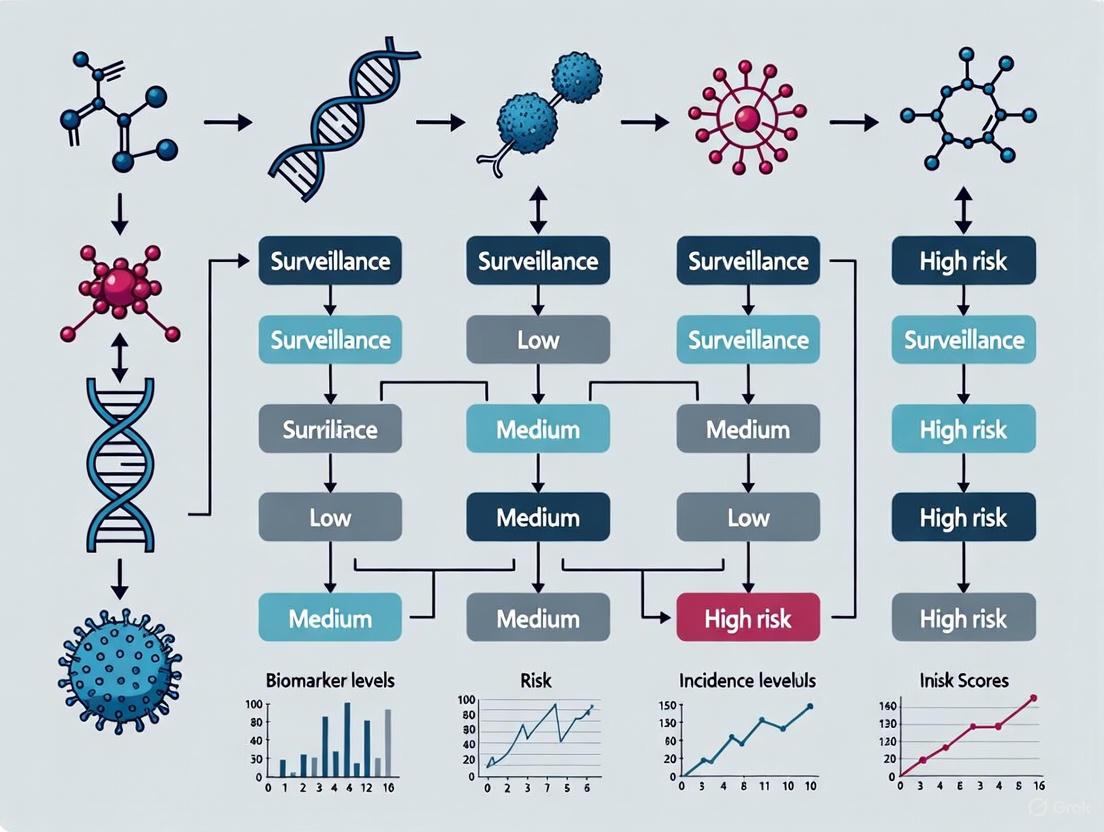
Spatial Optimization Surveillance Workflow
Protocol 2: Risk-Based Quality Tolerance Limit Implementation
Purpose: To establish and monitor Quality Tolerance Limits (QTLs) for critical trial parameters, enabling proactive risk-based surveillance focused on variables most impacting participant safety and data reliability.
Materials and Reagents:
- Clinical trial protocol with identified critical data and processes
- Historical benchmark data from similar trials
- Statistical process control software
- Centralized monitoring platform with visualization capabilities
- Predefined key risk indicators (KRIs)
Methodology:
- Criticality Assessment: Identify critical-to-quality factors essential to participant safety and trial conclusions through systematic process mapping and risk assessment.
- QTL Establishment: Define acceptable variability ranges for each parameter using historical data, therapeutic area standards, and clinical rationale.
- Monitoring Framework: Implement statistical surveillance to track parameter performance against QTLs, with automated alerts for breaches or trend violations.
- Escalation Protocol: Establish graded response procedures for QTL breaches based on severity, including root cause analysis and corrective/preventive actions.
- Effectiveness Evaluation: Periodically assess QTL performance in identifying meaningful issues, refining limits based on accumulating trial experience.
Implementation Considerations:
- QTLs should focus on parameters with direct impact on participant safety or trial conclusions rather than convenient but non-critical metrics.
- Tolerance limits should balance sensitivity (detecting real problems) with specificity (avoiding excessive false alarms) to maintain monitoring efficiency.
- The QTL framework should be dynamic, with periodic reassessment of limit appropriateness as trial experience accumulates.
Table 3: Risk-Based Monitoring Implementation Toolkit
| Tool Category | Specific Tools/Methods | Primary Function | Implementation Considerations |
|---|---|---|---|
| Risk Assessment Tools | Risk Assessment Categorization Tool (RACT), Failure Mode Effects Analysis (FMEA) | Systematic risk identification and prioritization | Involve multidisciplinary team; focus on patient safety and data integrity |
| Centralized Monitoring Tools | Statistical surveillance algorithms, Data visualization dashboards | Remote detection of anomalous patterns across sites | Validate against known issues; establish clear triggers for on-site follow-up |
| Key Risk Indicators | Screening failures, Protocol deviations, Informed consent errors | Early warning of emerging site issues | Benchmark against similar studies; adjust for site-specific factors |
| Quality Tolerance Limits | Eligibility violations, Primary endpoint data quality, SAE reporting timeliness | Define acceptable performance variability | Establish based on scientific rationale; review periodically for appropriateness |
| Source Document Verification Tools | Targeted SDV planners, Risk-based SDV algorithms | Focus verification on critical data elements | Identify critical observations; avoid 100% SDV unless justified |
The Scientist's Toolkit: Essential Reagents and Materials
Implementing effective risk-based surveillance requires both methodological frameworks and practical tools. This toolkit summarizes essential components for establishing modern, ethics-aligned surveillance systems in clinical research and early detection contexts.
Table 4: Essential Research Reagent Solutions for Risk-Based Surveillance
| Reagent/Material | Specifications | Functional Role | Application Context |
|---|---|---|---|
| Spatial Modeling Software | GIS capabilities, Stochastic simulation, Network analysis | Models threat introduction and spread pathways | Optimizing surveillance site selection for early detection |
| Statistical Process Control Tools | Real-time analytics, Visualization dashboards, Alert algorithms | Monitors key risk indicators and quality tolerance limits | Centralized monitoring of clinical trial parameters |
| Diagnostic Sensitivity Standards | Validated detection limits, Quantitative performance metrics | Establishes minimum performance requirements for detection methods | Ensuring surveillance methods can identify threats at acceptable prevalence |
| Data Governance Framework | Audit trail specifications, Access control protocols, Retention policies | Ensures data integrity, confidentiality, and reliability | Implementing ICH E6(R3) data governance requirements |
| Risk Assessment Categorization Tool | Risk scoring algorithm, Criticality weighting factors | Systematically identifies and prioritizes risks | Initial risk assessment for clinical trial monitoring planning |
| Digital Health Technologies | eConsent platforms, Wearable sensors, Telemedicine interfaces | Enables decentralized trial conduct and remote data collection | Implementing patient-centric, efficient trial designs |
The evolution from the Hippocratic Oath to ICH E6(R3) guidelines demonstrates how medicine has maintained its ethical foundation while systematically addressing increasingly complex challenges. The core commitment to patient benefit articulated in ancient Greece remains recognizable in modern risk-based surveillance approaches, though now implemented through sophisticated methodological frameworks. Contemporary clinical research oversight has transformed the physician's individual ethical commitment into systematically implemented, evidence-based surveillance strategies that protect participants across global research networks.
The successful implementation of risk-based surveillance requires both methodological rigor and ethical commitment. As demonstrated in the experimental protocols, optimal surveillance strategies often diverge from intuitive approaches—sometimes distributing resources across multiple moderate-risk locations outperforms concentration solely on highest-risk sites [8]. This underscores the value of evidence-based surveillance optimization compared to tradition-based monitoring approaches. Furthermore, the integration of ethical considerations throughout surveillance design ensures that efficiency gains do not come at the cost of participant protection or data integrity.
Looking forward, the principles of risk-based surveillance will continue to evolve alongside technological and methodological innovations. The implementation of ICH E6(R3) in 2025 represents not an endpoint but a milestone in the ongoing refinement of research oversight. As decentralized trials, digital health technologies, and novel methodologies advance, surveillance strategies must adapt while maintaining their foundational commitment to the ethical principles first articulated millennia ago. This continuous evolution ensures that medical research can efficiently generate reliable evidence while steadfastly protecting those who volunteer to participate in advancing medical knowledge.
Effective risk-based surveillance is fundamental to modern drug development, enabling the proactive detection of safety signals and ensuring public health. This framework is built on three interdependent core principles: risk assessment, the systematic process of identifying and analyzing potential risks; risk control, the measures implemented to modify those risks; and risk communication, the strategic sharing of information about risks to guide decision-making. Together, these principles form a continuous cycle that allows researchers and regulatory scientists to monitor products throughout their lifecycle, from clinical trials to post-market surveillance. A robust understanding of these elements is crucial for developing effective early detection research strategies that can adapt to emerging data in a dynamic regulatory environment [11] [12].
Risk Assessment: The Foundational Element
Definition and Purpose
Risk assessment is the structured process of identifying, analyzing, and evaluating potential uncertainties that could impact an organization's objectives, operations, or assets [13] [14] [15]. In the context of drug surveillance, it involves the evaluation of risks considering potential direct and indirect consequences of an incident, known vulnerabilities, and general or specific threat information [11]. This process provides the evidence base for proactive planning, allowing research scientists to allocate resources effectively and respond with agility rather than reacting to crises [15]. A well-executed assessment is documented, reproducible, and defensible to ensure transparency and practicality for stakeholders and decision-makers [11].
Core Components and Process
The risk assessment process consists of three core components executed through a series of defined steps.
Core Components:
- Risk Identification: The process of discovering what could go wrong, considering prime assets and how they could be impacted [14]. Techniques include stakeholder interviews, data classification analysis, and reviewing threat intelligence feeds [14].
- Risk Analysis: A deeper investigation into the level of risk associated with each identified threat using qualitative or quantitative methods to estimate likelihood and impact [14].
- Risk Evaluation: Determining how each identified risk should be handled by comparing potential impact and likelihood against the organization's risk tolerance to decide if it requires immediate mitigation [14].
Process Workflow:
The logical sequence of the risk assessment process is systematically mapped from context establishment through to mitigation planning. This workflow establishes the foundation for all subsequent risk management activities by transforming identified risks into actionable treatment strategies.
Quantitative and Qualitative Methodologies
Researchers must select appropriate assessment methodologies based on data availability, regulatory requirements, and the nature of risks. The following table compares the primary approaches:
Table: Comparison of Risk Assessment Methodologies
| Methodology | Definition / Approach | Best Application | Key Trade-Offs |
|---|---|---|---|
| Qualitative Assessment | Uses descriptive labels (High, Medium, Low) based on subjective judgment and expert opinion [14] [15]. | Situations with limited data or when quick prioritization is needed; effective for hard-to-quantify risks like reputational damage [15]. | Simple and fast but lacks precision; results can be subjective and potentially inconsistent [15]. |
| Quantitative Assessment | Uses numerical data, mathematical models (e.g., Monte Carlo simulations), and statistical methods to calculate risks [14] [15]. | Mature risk environments with sufficient data for detailed financial or statistical modeling; ideal for cost-benefit analysis [15]. | Highly precise and transparent but requires reliable data and technical modeling expertise; can be time-consuming [15]. |
| Semi-Quantitative Assessment | Blends numeric scoring (e.g., 1-10 scales) with qualitative judgment; often visualized via risk matrices [15]. | Teams needing more structure than qualitative offers but lacking resources for full quantitative analysis [15]. | More standardized than qualitative alone but still involves subjective bias; may create false sense of precision [15]. |
| Scenario Analysis (What-If) | Structured brainstorming to develop threat/hazard scenarios and assess likelihood and consequences [11]. | Developing strategy for managing risk from identified scenarios; useful for unusual or emerging risks [11]. | Creative and comprehensive but can be time-intensive; dependent on participant expertise [11]. |
Experimental Protocol: Conducting a Qualitative Risk Assessment for a Clinical Trial
Protocol Title: Qualitative Risk Assessment for Clinical Trial Safety Surveillance
Purpose: To systematically identify, analyze, and prioritize potential safety risks in a clinical trial setting using expert judgment to inform monitoring strategies.
Materials and Reagents:
- Risk Register Template: Digital or physical template for logging identified risks with descriptions, categories, and proposed controls [14].
- Risk Assessment Matrix: A visual grid tool (typically 5x5) that categorizes risks based on likelihood and impact [14].
- Stakeholder List: Comprehensive list of clinical, regulatory, and scientific experts to interview.
- Data Sources: Previous clinical trial data, literature on similar compounds, pre-clinical findings, and known class effects.
Procedure:
- Establish Context: Define the assessment's scope (e.g., Phase III trial for novel oncology therapeutic), objectives, and key stakeholders including pharmacovigilance, clinical development, and biostatistics team members [14].
- Risk Identification: a. Conduct structured interviews and workshops with stakeholders. b. Document all potential safety risks (e.g., specific adverse events, drug interactions, population-specific risks) in the risk register. c. Utilize "what-if" analysis for unusual or emerging risks not evident from historical data [11].
- Risk Analysis: a. For each identified risk, convene an expert panel to score likelihood (e.g., Rare to Almost Certain) and impact (e.g., Insignificant to Catastrophic) using predefined scales. b. Plot each risk on the risk matrix to determine its initial rating (e.g., Low, Medium, High, Extreme) [14].
- Risk Evaluation: a. Prioritize risks based on their matrix positioning. b. Compare prioritized risks against the organization's risk appetite to determine which require immediate control measures [14] [12].
- Documentation: a. Record all findings, including the rationale for scores and priorities. b. Present the finalized risk register and matrix to decision-makers for resource allocation [14].
Risk Control: Implementing Protective Measures
Definition and Purpose
Risk control encompasses the strategies, procedures, and measures utilized to modify risk by reducing its likelihood, impact, or velocity (the speed at which a risk escalates) [16] [17]. These are essential measures that an organization implements to minimize, mitigate, or manage risk levels, enabling operations within established risk appetite boundaries [12]. Controls actively intervene in risk factors that could impact an organization's objectives, with the goal of either decreasing the likelihood of risks occurring or minimizing their potential impact [16]. In pharmaceutical surveillance, effective controls are critical for ensuring that potential safety issues are contained before they can affect patient populations.
Types of Risk Controls
Controls are categorized based on their point of application in the risk lifecycle, each serving a distinct function in modifying risk characteristics:
Primary Control Categories:
Comprehensive Control Approaches: Beyond the primary categories, organizations employ several strategic approaches to risk control:
- Risk Avoidance: Eliminating exposure to a risk factor entirely, such as halting a clinical trial due to emerging safety signals [12].
- Loss Prevention: Implementing measures to reduce and prevent losses, such as surveillance protocols and systematic data monitoring [12].
- Loss Reduction: Limiting the extent of loss that may occur, exemplified by implementing additional patient monitoring for known adverse events [12].
- Risk Separation: Limiting risk exposure spread across locations, such as geographic diversification of manufacturing sites to ensure supply continuity [12].
Experimental Protocol: Developing a Control Register for Drug Safety Surveillance
Protocol Title: Creation and Maintenance of a Risk Control Register for Pharmacovigilance
Purpose: To systematically document, track, and test controls implemented to mitigate identified drug safety risks, ensuring they remain effective and aligned with risk appetite.
Materials and Reagents:
- Control Register Template: Digital repository (e.g., GRC software or database) for recording control details [12].
- Risk Register: Previously documented list of identified and prioritized risks [12].
- Testing Framework: Questionnaires, inspection checklists, and data analysis procedures for control validation.
- Effectiveness Metrics: Key Risk Indicators (KRIs) and operational data to measure control performance.
Procedure:
- Control Identification: a. For each risk in the risk register, identify existing and proposed controls. b. Categorize each control as preventive, detective, or reactive [16] [17]. c. Limit registered controls to key and medium controls (typically 2-4 per risk) to maintain focus [17].
- Control Documentation: a. In the control register, capture for each control: name, description, type, owner, purpose, related risk, frequency of application, implementation status, and testing frequency [12]. b. Ensure each control is directly mapped to the specific risk(s) it modifies [12].
- Effectiveness Testing: a. Establish a regular schedule for control testing based on the organization's needs and risk nature [12]. b. Employ multiple testing methods: questionnaires, observations, inspections, and review of relevant documents and records [12]. c. Document testing results and any identified weaknesses.
- Performance Monitoring: a. Leverage operational data (e.g., adverse event reports, compliance metrics) to assess if controls are maintaining risk within tolerable levels [12]. b. Use integrated GRC platforms to map controls to incident data and KRIs for real-time monitoring [12].
- Optimization: a. Analyze control strengths and weaknesses alongside cost-effectiveness [12]. b. Adjust or replace ineffective controls based on testing results and performance data. c. Regularly reassess the control register to reflect changes in the risk landscape.
Risk Communication: Strategic Information Exchange
Definition and Purpose
Risk communication is a strategic, two-way process of sharing information about risks and benefits to facilitate optimal decision-making [18]. For regulatory agencies and pharmaceutical companies, it involves communicating "frequently and clearly about risks and benefits—and about what organizations and individuals can do to minimize risk" [18]. In drug development, this means providing healthcare professionals, patients, and consumers with the information they need about regulated products in an accessible format and timely manner to ensure appropriate use [18]. Effective communication is not merely about disseminating information but ensuring comprehension and enabling informed choices that protect public health.
Core Principles and Strategic Framework
Effective risk communication follows several guiding principles: it must be integral to organizational mission, adapted to various audience needs, and continuously evaluated for optimal effectiveness [18]. The U.S. FDA's Strategic Plan for Risk Communication outlines a comprehensive framework built on three pillars with associated strategies:
Table: Strategic Framework for Risk Communication
| Strategic Area | Key Strategies |
|---|---|
| Strengthening Science | 1. Identify and fill gaps in risk communication knowledge.2. Evaluate effectiveness of risk communication activities.3. Translate knowledge gained through research into practice [18]. |
| Expanding Capacity | 1. Streamline message development and coordination.2. Plan for crisis communications.3. Improve two-way communication through enhanced partnerships.4. Increase staff with behavioral science expertise [18]. |
| Optimizing Policy | 1. Develop principles for consistent and easily understood communications.2. Identify consistent criteria for when and how to communicate emerging risk information.3. Assess and improve communication policies in high public health impact areas [18]. |
Communication Channels and Tools
Pharmaceutical companies and regulators employ multiple channels to communicate risk information, each serving distinct purposes and audiences:
- Labeling Tools: Summary of Product Characteristics (SmPC), package inserts, patient information leaflets (PILs), and carton labeling represent primary, regulated communication channels [19].
- Direct Communications: "Dear Healthcare Professional Communications" disseminate important safety information directly to prescribers [19].
- Public Health Advisories: FDA Drug Safety Communications provide timely information about new safety issues to patients and healthcare professionals to support informed treatment decisions [20].
- Digital Platforms: Web sites and web tools serve as primary mechanisms for communicating with different stakeholders, requiring continuous optimization for usability and accessibility [18].
Experimental Protocol: Developing a Risk Communication Strategy for an Emerging Safety Signal
Protocol Title: Protocol for Developing a Targeted Risk Communication Plan
Purpose: To create and evaluate a strategic communication plan for conveying emerging risk information about a medicinal product to relevant stakeholders, maximizing comprehension and appropriate action.
Materials and Reagents:
- Audience Analysis Templates: Profiles for healthcare professionals, patients, and caregivers detailing information needs, literacy levels, and preferred channels.
- Message Mapping Tools: Frameworks for developing consistent, clear, and concise core messages.
- Testing Materials: Draft communications, survey questionnaires, and focus group guides for message testing.
- Dissemination Checklist: Inventory of communication channels (regulatory documents, direct communications, public announcements, digital platforms).
Procedure:
- Situation Analysis: a. Constitute a dedicated communications group with relevant expertise to coordinate strategy [19]. b. Gather all available data on the emerging safety signal, including evidence quality, populations at risk, and clinical implications.
- Audience Assessment: a. Identify and segment target audiences (e.g., prescribing specialists, primary care physicians, patients with specific comorbidities). b. For each segment, analyze their specific information needs, pre-existing knowledge, and potential concerns [18].
- Message Development: a. Develop core messages explaining the risk, context, evidence strength, and recommended actions. b. Apply principles for consistent and easily understood communications, avoiding absolute terms and explaining the benefit-risk context [18]. c. Test draft messages with representative audience samples and refine based on feedback [18].
- Channel Selection and Dissemination: a. Select appropriate channels for each audience (e.g., Drug Safety Communications for HCPs, patient-friendly materials for the public) [20]. b. Coordinate internal reviews and simultaneous release to ensure message consistency [19]. c. Implement dissemination according to the plan, utilizing multiple channels for reinforcement.
- Effectiveness Evaluation: a. Monitor audience reaction through surveys, media analysis, and tracking of relevant health metrics [18] [19]. b. Assess comprehension levels and behavioral changes following communication. c. Adjust future communications based on evaluation findings and emerging data.
The Scientist's Toolkit: Essential Research Reagents and Materials
Table: Essential Resources for Risk-Based Surveillance Research
| Tool / Resource | Function / Purpose | Application Context |
|---|---|---|
| Risk Register Template | Digital or physical template for systematically logging identified risks, with descriptions, categories, and proposed controls [14]. | Serves as the central repository during risk identification and assessment phases across all research domains. |
| Risk Assessment Matrix | A visual grid tool (typically 5x5) that categorizes risks based on their assessed likelihood and impact [14]. | Used during risk analysis and evaluation to determine risk priority levels and inform resource allocation decisions. |
| GRC Software | Governance, Risk, and Compliance platforms provide a centralized system for managing risks, controls, assessments, and incident data [12]. | Automates the risk management process, enables real-time monitoring, and facilitates reporting and visualization for stakeholders. |
| Control Register | A log used to document and track controls across an enterprise, directly linked to the organization's risk register [12]. | Essential for control management, testing scheduling, and maintaining an audit trail of risk mitigation efforts. |
| Stakeholder List | Comprehensive inventory of clinical, regulatory, and scientific experts, along with patients or community representatives. | Used throughout the risk management process to ensure appropriate input, validation, and communication with all relevant parties. |
| Message Testing Materials | Draft communications, survey questionnaires, and focus group guides for evaluating message clarity and effectiveness [18]. | Critical for pre-launch validation of risk communications to ensure target audiences correctly interpret safety information. |
In the fields of public health, plant protection, and clinical drug development, the imperative for early detection of adverse events is paramount. Traditionally, surveillance has operated on a model of standardized, periodic monitoring. However, this approach is increasingly being supplanted by risk-based paradigms that strategically focus resources where they are most likely to detect problems. A traditional surveillance system is characterized by its reactive, scheduled, and broad-based application, whereas a risk-based system is proactive, adaptive, and targeted [21]. This shift is driven by the recognition that uniform surveillance is often inefficient, missing early warning signs in populations or processes with elevated risk. The consequences of delayed detection can be severe, ranging from uncontrolled disease outbreaks in animal populations [21] and devastated agricultural industries [9] to compromised data integrity and patient safety in clinical trials [22].
The core thesis of this proactive shift is that risk-based surveillance strategies significantly enhance the sensitivity and efficiency of early detection systems. By integrating quantitative risk assessments and dynamic resource allocation, these paradigms offer a more powerful framework for identifying threats before they escalate. This document provides detailed application notes and experimental protocols to guide researchers and drug development professionals in implementing and optimizing these advanced surveillance strategies.
Comparative Analysis: Traditional vs. Risk-Based Surveillance
The following table summarizes the fundamental contrasts between the two surveillance paradigms, highlighting the operational and philosophical differences.
Table 1: Core Contrasts Between Traditional and Risk-Based Surveillance Paradigms
| Feature | Traditional Surveillance | Risk-Based Surveillance |
|---|---|---|
| Core Philosophy | Reactive, uniform coverage | Proactive, targeted based on threat |
| Resource Allocation | Fixed, evenly distributed | Dynamic, focused on high-risk units |
| Data Utilization | Relies on scheduled data collection | Leverages real-time data and risk indicators |
| Key Strength | Simple to design and implement | Higher sensitivity and efficiency for early detection |
| Primary Limitation | Can miss emerging threats in blind spots | Requires sophisticated risk assessment and analysis |
| Example in Clinical Trials | 100% Source Data Verification (SDV) | Centralized monitoring focused on critical data points [22] |
| Example in Pathogen Detection | Periodic, random sampling across a landscape | Surveillance optimized to maximize probability of detecting an invading pathogen [9] |
Quantitative evidence demonstrates the rapid adoption and efficacy of risk-based approaches. In clinical trials, implementation of at least one Risk-Based Quality Management (RBQM) component surged from 53% of trials in 2019 to 88% in 2021 [22]. This shift is driven by the ability of risk-based methods to improve trial outcomes, enhance data quality, and optimize resource allocation in an increasingly complex clinical research landscape [23].
Application Note: Implementing Risk-Based Surveillance for Early Detection
Core Principles and Workflow
Implementing a risk-based surveillance system is a structured process that moves from risk identification to continuous optimization. The core workflow can be visualized as a cycle of key activities, as shown in the following diagram.
Diagram 1: The RBQM Continuous Cycle. This workflow illustrates the iterative process of risk-based quality management, from defining objectives to continuous optimization based on feedback.
The foundation of this paradigm is the identification of Critical to Quality (CTQ) factors—the processes and data points most essential to patient safety and data integrity [23]. This is followed by continuous risk assessment and targeted resource deployment. A critical insight from epidemiological modelling is that optimal surveillance does not always mean focusing solely on the very highest-risk site. When risk is spatially correlated, "putting all your eggs in one basket" can be suboptimal; spreading resources according to a calculated strategy can maximize the overall probability of detection [9].
Quantitative Framework for Sensitivity
A key advantage of the risk-based paradigm is the ability to quantify surveillance system sensitivity (SSe). For early disease detection, SSe can be conceptualized as a function of three components [21]:
- Population Coverage: The proportion of the population under surveillance.
- Temporal Coverage: The frequency of observation or testing.
- Detection Sensitivity: The ability to identify the target once a unit is surveyed.
This quantitative framework allows for direct comparison of different surveillance system designs. Expert elicitation panels can be used to weight specific system traits—such as observation frequency, clarity of reporting guidance, and observer incentives—to build a replicable model for estimating SSe in observational surveillance [24]. This model can then inform both early detection design and the confidence in disease freedom provided by negative surveillance reports.
Experimental Protocols
Protocol 1: Designing a Risk-Based Surveillance Network for Pathogen Detection
This protocol provides a methodology for optimizing the physical arrangement of surveillance sites to maximize the probability of early pathogen detection, adaptable for plant, animal, or public health applications.
4.1.1 Research Reagent Solutions
Table 2: Essential Materials for Spatial Surveillance Optimization
| Item | Function |
|---|---|
| Spatially Explicit Host Data | Provides a landscape map of host population density and distribution, the foundation for modeling spread and risk. |
| Pathogen Entry & Spread Model | A stochastic, simulation model to replicate the introduction and spread of the pathogen through the host landscape. |
| Stochastic Optimization Routine | A computational algorithm (e.g., Monte Carlo) to identify surveillance site arrangements that maximize detection probability. |
| Diagnostic Sensitivity Parameter | The known probability that a test will correctly identify an infected host, used to calibrate the detection model. |
4.1.2 Methodology
Model Parameterization:
- Acquire or develop a high-resolution, spatially explicit map of the host population (e.g., citrus tree density for Huanglongbing surveillance) [9].
- Develop a stochastic model simulating pathogen entry at likely introduction points (e.g., ports, high-traffic areas) and subsequent spread through the host landscape. The model should run until a predefined, maximum acceptable prevalence is exceeded.
Integration of Detection Module:
- Couple the epidemiological model with a statistical detection module. This module should incorporate logistical parameters, including the number of surveillance sites, survey frequency, and the diagnostic sensitivity of the detection method.
Optimization Execution:
- Use a stochastic optimization algorithm to test thousands of potential surveillance site arrangements.
- The algorithm should select the arrangement of sites that maximizes the probability of detecting the pathogen before the outbreak reaches the maximum acceptable prevalence threshold.
Validation and Comparison:
- Compare the performance (probability of detection and cost) of the optimized surveillance network against conventional, static risk-based targeting.
- Validate the model's recommendations against historical outbreak data, if available.
The following workflow diagram illustrates the key computational steps in this protocol.
Diagram 2: Pathogen Surveillance Optimization. A computational workflow for designing a surveillance network that maximizes early detection probability for an invading pathogen.
Protocol 2: Implementing a Risk-Based Quality Management (RBQM) System in Clinical Trials
This protocol outlines the steps for integrating an RBQM system into a clinical trial, aligning with ICH E6(R2) and E8(R1) guidelines and modern regulatory expectations [22] [23].
4.2.1 Research Reagent Solutions
Table 3: Essential Components for a Clinical RBQM System
| Item | Function |
|---|---|
| Centralized Monitoring Platform | A technology platform that enables remote, real-time oversight of clinical site data, facilitating risk identification across sites. |
| Risk Assessment Tool | A standardized framework (e.g., weighted checklist, software) for conducting initial and ongoing cross-functional risk assessments. |
| Key Risk Indicator (KRI) Dashboard | A visual interface that tracks predefined metrics (KRIs) to signal potential emerging issues at clinical sites. |
| Quality Tolerance Limit (QTL) Framework | Predefined boundaries for acceptable variation in critical study parameters, used to trigger corrective actions. |
4.2.2 Methodology
Initial Cross-Functional Risk Assessment:
- Convene a team including representatives from clinical operations, data management, biostatistics, and safety.
- Identify Critical to Quality (CTQ) factors: Determine the critical processes and data points essential to trial integrity and participant safety (e.g., primary endpoint data, informed consent process, adherence to inclusion/exclusion criteria) [23].
- Identify and evaluate risks: For each CTQ factor, brainstorm potential risks. Evaluate each risk based on its probability of occurrence and its impact on patient safety and data reliability.
- Develop mitigation strategies: For each high-risk item, define a proactive mitigation plan. This may include specialized training, enhanced monitoring, or protocol clarification.
Define Monitoring Triggers:
- Establish Quality Tolerance Limits (QTLs): Set statistical boundaries for key study metrics (e.g., screen failure rate, rate of protocol deviations). Exceeding a QTL triggers a formal investigation.
- Define Key Risk Indicators (KRIs): Identify leading indicators of potential problems (e.g., rate of data entry lag, frequency of specific adverse events) and configure the centralized monitoring platform to track them via a dashboard.
Execute Centralized and Targeted On-Site Monitoring:
- Reduce Source Data Verification (SDV): Move away from 100% SDV. Instead, use centralized monitoring to review all site data and target SDV to critical data points or sites flagged by KRIs/QTLs [22].
- Focus on-site visits: Use insights from centralized monitoring to plan targeted, on-site visits that investigate root causes of issues rather than performing exhaustive data checks.
Ongoing Review and Adaptation:
- Hold regular, cross-functional meetings to review KRIs, QTL status, and the overall risk landscape.
- Adapt the risk management plan as the trial progresses and new risks are identified, ensuring the system remains dynamic and responsive.
The logical flow of risk identification, control, and review in an RBQM system is depicted below.
Diagram 3: Clinical RBQM Logic. The continuous loop of risk management in clinical trials, from initial assessment to adaptive control.
The evidence from diverse fields—clinical research, animal health, and plant pathology—converges on a single conclusion: the proactive, risk-based paradigm is fundamentally superior to traditional surveillance for the purpose of early detection. The shift from a reactive, uniform approach to a dynamic, targeted strategy represents a maturation of surveillance science. It is a shift from merely looking to seeing, and from simply collecting data to deriving intelligence.
The protocols outlined herein provide a tangible roadmap for researchers and drug development professionals to implement this paradigm. By quantifying system sensitivity, strategically allocating resources, and leveraging continuous feedback loops, risk-based surveillance enhances our capacity to detect threats at the earliest possible moment. This not only safeguards health and health data but also generates significant efficiency and cost savings. As clinical trials grow more complex and global pathogen pressures intensify, the adoption of these sophisticated surveillance strategies transitions from a best practice to an indispensable component of responsible research and public health protection.
Global Regulatory Alignment and Remaining Discrepancies
Risk-based surveillance represents a strategic approach to early disease detection in which resources are preferentially allocated to subpopulations, geographical areas, or pathways classified as high-risk for disease introduction or spread [8] [25]. This methodology intentionally introduces selection bias to optimize the probability of detecting diseases or infections when resources are limited [25] [26]. For researchers and drug development professionals, understanding the interplay between evolving global regulatory frameworks and the epidemiological principles of risk-based surveillance is critical for designing effective early detection systems for emerging health threats.
The fundamental objective of risk-based surveillance is to achieve higher benefit-cost ratios with existing or reduced resources by focusing on units with the greatest likelihood of disease presence [26]. These systems apply risk assessment methods at various stages of traditional surveillance design to enhance early detection and management of diseases or hazards [26]. In practice, this requires navigating an increasingly complex global regulatory environment characterized by both harmonization initiatives and persistent jurisdictional fragmentation.
Current Regulatory Frameworks: Alignment Initiatives and Persistent Gaps
International Regulatory Convergence
Global regulatory alignment has seen significant advances through international organizations and agreements that establish shared standards and principles. The World Trade Organization (WTO) remains the primary mediator of trade between nations, balancing exports and imports, while the International Monetary Fund (IMF) establishes frameworks for international economic cooperation [27]. The Organisation for Economic Co-operation and Development (OECD) addresses economic and social challenges through policy coordination, and regional blocs like the European Union and USMCA have strengthened policies to promote fairer trade [27].
Substantive alignment has occurred in several key areas:
- Financial Action Task Force (FATF) Recommendations: Provide near-global standards for anti-money laundering and counter-terrorist financing practices, though implementation varies [28]
- Basel III frameworks: International banking regulations that have achieved significant cross-border adoption [28]
- EU AI Act: Establishing a risk-based framework for artificial intelligence with tiered obligations based on system classification [27]
Areas of Significant Regulatory Divergence
Despite convergence in certain domains, significant regulatory fragmentation persists across jurisdictions, creating operational complexity for global research and surveillance initiatives.
Table 1: Key Areas of Regulatory Divergence Impacting Global Surveillance
| Domain | Nature of Divergence | Impact on Surveillance Programs |
|---|---|---|
| Artificial Intelligence Governance | EU adopts comprehensive risk-based framework (AI Act) while other regions implement sector-specific guidelines [27] | Creates compliance complexity for AI-powered diagnostic tools and surveillance algorithms |
| Data Privacy & Transfer | GDPR-inspired regulations versus region-specific frameworks (e.g., India's DPDPA-2023) with differing data localization requirements [27] [28] | Restricts cross-border data sharing essential for global disease surveillance |
| Anti-Money Laundering (AML) | Each country maintains unique requirements despite FATF guidelines, creating overlapping and sometimes contradictory rulesets [28] | Complicates financial transactions supporting international research collaborations |
| Digital Assets | Fragmented rulebooks with different regional priorities without coordinated implementation [28] | Hinders development of blockchain-based surveillance data systems |
This regulatory fragmentation creates substantial operational challenges for organizations implementing global surveillance systems. Companies face duplicated compliance efforts across jurisdictions, manual and inconsistent regulatory interpretations, language barriers requiring local expertise, and difficulty maintaining centralized views of global obligations [28]. The financial impact includes costs for hiring legal experts in each market, implementing compliance tracking systems, continuous employee training, and third-party audits [27].
Methodological Framework: Risk-Based Surveillance Protocols
Core Principles and Definitions
Risk-based surveillance systems are defined as those that apply risk assessment methods in different steps of traditional surveillance design for early detection and management of diseases or hazards [26]. The principal objectives include identifying surveillance needs to protect health, setting priorities, and allocating resources effectively and efficiently [26].
The epidemiological foundation relies on appropriate risk quantification. For risk-based surveillance, crude (unadjusted) relative risk or odds ratio estimates are preferable to adjusted estimates, as units are selected based on the presence of specific risk factors regardless of other potential confounders [25]. This represents the total (unadjusted) risk encompassing both causal and non-causal associations relevant to practical sampling situations [25].
Experimental Protocol: Optimizing Spatial Surveillance Design
The following protocol provides a methodology for designing risk-based surveillance systems that explicitly account for pathogen entry and spread dynamics, adapted from Mastin et al.'s approach for detecting invasive plant pathogens [8] [9].
Materials and Equipment
Table 2: Research Reagent Solutions for Surveillance Optimization
| Item | Specification | Function/Application |
|---|---|---|
| Spatial Host Density Data | High-resolution geographical data on host distribution (e.g., citrus density maps for HLB surveillance) [8] | Informs risk model parameterization and surveillance site selection |
| Pathogen Dispersal Kernel | Exponential or power-law models parameterized from empirical spread data [8] | Predicts spatial spread patterns from introduction points |
| Diagnostic Sensitivity Parameters | Test performance characteristics (probability of detection) for available diagnostic methods [8] [29] | Informs sampling intensity requirements and detection probabilities |
| Stochastic Optimization Algorithm | Computational method (e.g., simulated annealing) for site selection [8] | Identifies surveillance arrangements maximizing detection probability |
| Risk-Based Sampling Framework | Protocol for preferential sampling of high-risk strata [25] [26] | Enhances detection probability through targeted resource allocation |
Procedure
Step 1: Landscape Parameterization
- Obtain or develop a gridded landscape (e.g., 1 km × 1 km cells) containing density data for relevant hosts [8]
- Parameterize secondary spread using an exponential dispersal kernel fitted to available pathogen spread data [8]
- Define pathogen introduction rates and locations based on known risk pathways (e.g., human movement patterns from infected areas) [8]
Step 2: Simulation Model Implementation
- Develop a spatially explicit, stochastic model simulating pathogen entry and spread through the landscape
- Run multiple simulations (minimum 1,000 iterations) until a predefined maximum acceptable prevalence threshold is exceeded [8]
- Record timing and location of infections for each simulation run
Step 3: Detection Modeling
- Incorporate statistical models of detection that account for:
- Model increase in detectability following infection as deterministic processes based on known pathogen dynamics [8]
Step 4: Surveillance Optimization
- Use stochastic optimization (e.g., simulated annealing) to identify surveillance site arrangements (Ω) that maximize probability of detection before prevalence threshold is reached [8]
- Constrain optimization by practical parameters:
- Validate that optimal strategy avoids over-concentration on single highest-risk sites when spatial correlation exists [8]
Step 5: Performance Evaluation
- Compare optimized surveillance strategy performance against conventional risk-based approaches [8]
- Calculate performance gain and potential cost savings [8]
- Conduct sensitivity analysis on key parameters (introduction location, diagnostic sensitivity, sampling frequency) [8]
Workflow Visualization
Diagram 1: Risk-based surveillance design workflow
Regulatory Navigation Protocol: Managing Cross-Border Compliance
Technology-Enabled Compliance Framework
Modern regulatory change management requires systematic processes to monitor, assess, adapt to, and comply with evolving international requirements [27]. The following protocol leverages RegTech solutions to maintain compliance across fragmented regulatory landscapes.
Materials
- Governance, Risk, and Compliance (GRC) software with API access to 400+ global data sources [28]
- Automated regulatory tracking systems monitoring specialized websites, agency portals, and regulator communications [27]
- AI-powered platforms capable of parsing regulatory documents across multiple languages [28]
- Control mapping systems linking requirements across frameworks [27]
Procedure
Step 1: Regulatory Change Monitoring
- Implement automated monitoring of regulatory updates across all relevant jurisdictions [27]
- Configure AI systems to extract obligations with context from regulatory documents [28]
- Establish knowledge graphs connecting obligations to internal policies, controls, and products [28]
Step 2: Impact Assessment and Gap Analysis
- Conduct thorough analysis of operational, procedural, and compliance implications for each regulatory change [27]
- Perform gap analysis comparing existing policies with new requirements [27]
- Document discrepancies and associated risks, prioritizing by risk level [27]
Step 3: Control Mapping and Implementation
- Map controls across multiple regulatory frameworks to eliminate redundancies [27]
- Develop action plans with resource allocation, timelines, and priorities based on urgency [27]
- Update internal policies and controls to address identified gaps [27]
Step 4: Continuous Compliance Monitoring
- Implement automated dashboards providing real-time compliance status [27]
- Establish continuous monitoring systems flagging non-compliance proactively [27]
- Maintain comprehensive documentation for regulatory reporting and audits [27]
Cross-Border Material Transfer Protocol
Diagram 2: Cross-border material transfer compliance
Discussion: Strategic Implications for Surveillance Research
The integration of risk-based surveillance principles with adaptive regulatory compliance creates powerful frameworks for early detection of emerging health threats. Research demonstrates that optimal surveillance strategies must account for complex spatial dynamics rather than simply targeting the highest-risk sites [8]. Specifically, spatial correlation in risk can make it suboptimal to focus solely on the highest-risk locations, necessitating strategic distribution of surveillance resources across multiple potential introduction sites [8].
The regulatory landscape continues to evolve toward what experts term a "regulatory tsunami," with increasingly stringent requirements across sectors [27]. While some regional harmonization occurs, geopolitical factors are driving further divergence in many domains [28]. Successful navigation of this environment requires organizations to invest in regulatory agility—the ability to adapt quickly to regulatory changes regardless of their origin [28].
For researchers developing surveillance systems, key considerations include:
- Diagnostic sensitivity impact: The optimal surveillance strategy differs depending on available detection methods and their sensitivity [8]
- Resource allocation trade-offs: The number of survey sites, sampling frequency, and samples per site interact to determine overall system performance [8] [29]
- Validation requirements: Risk-based surveillance systems must demonstrate equal or higher efficacy than traditional systems with higher efficiency (benefit-cost ratio) [26]
- Cross-border data sharing: Regulatory restrictions on data transfer may limit the effectiveness of international surveillance networks [27] [28]
Future developments in AI-powered regulatory technology show promise for alleviating compliance burdens through automated monitoring, control mapping, and continuous compliance assessment [27] [28]. However, the fundamental tension between globalized health threats and jurisdictional regulatory sovereignty will continue to present challenges for international surveillance initiatives.
From Theory to Practice: Implementing Advanced Risk-Based Frameworks
Risk-Based Quality Management (RBQM) is a systematic, proactive framework for managing quality in clinical trials by focusing efforts on factors critical to human subject protection and the reliability of trial results. The implementation of RBQM is championed by global regulatory bodies, including the FDA and EMA, and is codified in the ICH E6 (R2) and the upcoming ICH E6 (R3) guidelines [30] [31]. This approach represents a fundamental shift from reactive, error-correction models to a preventive strategy that prioritizes "errors that matter," thereby optimizing resource allocation and enhancing the overall quality and efficiency of clinical research [30].
Within the broader thesis of risk-based surveillance for early detection, RBQM provides a powerful operational model. Just as surveillance strategies in other fields (e.g., infectious disease control or cancer recurrence monitoring) aim to allocate resources based on risk to achieve early detection [32] [33], RBQM applies the same paradigm to clinical trial oversight. It advocates for a surveillance system within the trial that is adaptive, targeted, and data-driven, moving away from a one-size-fits-all frequency of monitoring visits and 100% data verification towards a model where oversight activities are continuously calibrated to the evolving risks of the study [34] [31]. This ensures that the greatest oversight is directed at the processes and data most critical to patient safety and the robustness of the trial's conclusions.
The Regulatory and Quantitative Landscape of RBQM Adoption
The regulatory impetus for RBQM began with the ICH E6 (R2) addendum, which introduced new sections on quality management and risk-based monitoring [31]. This addendum mandates that sponsors implement a quality management system where critical processes and data are identified, and risks are assessed and mitigated [34]. The forthcoming ICH E6 (R3) is expected to provide even greater support for these RBQM principles throughout the clinical trial lifecycle [35].
A recent Tufts Center for the Study of Drug Development (CSDD) survey provides a quantitative snapshot of RBQM adoption across the industry. The study, which assessed 32 distinct RBQM practices, found that, on average, companies have implemented RBQM in 57% of their clinical trials [35]. However, adoption varies significantly based on organizational size and experience.
Table 1: Adoption of RBQM Components in Clinical Trials (Based on Tufts CSDD Survey) [35]
| RBQM Component Category | Examples of Specific Components | Implementation Notes |
|---|---|---|
| Planning & Design | Identification of Critical-to-Quality factors, Risk Assessment, Protocol Complexity Assessment | Foundational activities; ~80% of trials implement the initial risk assessment [30]. |
| Execution | Key Risk Indicators (KRIs), Quality Tolerance Limits (QTLs), Statistical Data Monitoring, Reduced Source Data Verification (SDV) | Centralized monitoring techniques are key; adoption of other components beyond risk assessment is lower, ranging from 22-43% [30]. |
| Documentation & Resolution | Identification and Evaluation of Risks and QTL deviations, Updates to monitoring plans | Critical for continuous learning and system improvement. |
Table 2: Barriers to RBQM Adoption and Potential Mitigations [30] [35]
| Barrier Category | Specific Challenges | Potential Mitigation Strategies |
|---|---|---|
| Organizational & Knowledge | Lack of organizational knowledge and awareness, mixed perceptions of value proposition. | Secure executive sponsorship, appoint RBQM champions, and invest in cross-functional training [30]. |
| Process & Change Management | Poor change management planning, complexity of available solutions. | Follow a structured implementation roadmap (e.g., a 10-step process), start with pilot studies [30]. |
| Operational | Difficulties in integrating processes and technology across functions. | Select flexible, interoperable technology platforms and foster cross-functional ownership of RBQM [30]. |
Application Notes: Core Principles and Implementation Protocol
Successful implementation of RBQM relies on a cross-functional team and a structured, iterative process. The following protocol outlines the key stages.
Foundational Protocol: A Cross-Functional RBQM Implementation Workflow
This workflow details the continuous cycle of risk management in a clinical trial, from initial design through study closeout.
Phase 1: Pre-Study Planning & Risk Assessment
- Step 1: Define Critical-to-Quality (CtQ) Factors. A cross-functional team (e.g., clinical, data management, biostatistics, medical) must identify the few data and processes that are most critical to the scientific validity of the trial and to patient safety [30] [34]. These are the "errors that matter."
- Step 2: Conduct Risk Assessment. For each CtQ factor, the team identifies what could go wrong (risks), evaluates the likelihood and impact of those risks, and prioritizes them [34] [31]. A common tool for this is a risk log or a failure mode and effects analysis (FMEA).
- Step 3: Develop the RBQM Plan. This living document details:
- Risk Control Strategies: Actions to prevent or mitigate prioritized risks.
- Monitoring Strategy: The mix of centralized and on-site monitoring activities.
- Key Risk Indicators (KRIs): Proactive, quantifiable measures to monitor risk exposure (e.g., data entry timeliness, query rates, protocol deviation rates) [34].
- Quality Tolerance Limits (QTLs): Predefined thresholds for key study variables that, if breached, trigger a formal evaluation and action [34].
Phase 2: Study Execution & Centralized Monitoring
- Step 4: Implement Centralized Monitoring. This is the remote, timely evaluation of accumulating data from all sites [31]. It employs:
- Step 5: Conduct Targeted On-Site Monitoring. On-site activities are no longer focused on 100% Source Data Verification (SDV). Instead, visits are targeted based on triggers from centralized monitoring (e.g., a site with a KRI alert) and focus on verifying critical data and processes, training site staff, and investigating root causes of issues [30] [31].
Phase 3: Ongoing Review & Adaptive Action
- Step 6: Perform Periodic Cross-Functional Review. The study team regularly reviews data from centralized monitoring, KRIs, and QTLs to assess if the risk profile has changed and if control measures are effective [34] [35].
- Step 7: Trigger Corrective and Preventive Actions (CAPA). When a QTL is breached or a significant risk is identified, a root cause analysis is performed, and appropriate CAPA is implemented. This may include updating the RBQM plan, providing additional site training, or modifying data collection tools [31].
The Scientist's Toolkit: Essential Reagents for RBQM Implementation
Table 3: Key Research Reagent Solutions for RBQM
| Tool / Reagent | Category | Primary Function in the RBQM Experiment |
|---|---|---|
| RBQM Software Platform | Technology | Provides an integrated environment for risk planning, KRI/QTL tracking, statistical data monitoring, and generating centralized monitoring reports [30]. |
| Electronic Data Capture (EDC) | Technology | The primary system for clinical data collection; allows for real-time data validation and is a core data source for KRIs and centralized analyses [34]. |
| Clinical Trial Management System (CTMS) | Technology | Provides operational data (e.g., site activation, enrollment rates) that can be integrated into KRIs for comprehensive risk oversight [34]. |
| Risk Management Plan Template | Document | A standardized template (often an SOP) for documenting the initial risk assessment, CtQ factors, KRIs, QTLs, and mitigation strategies [34] [36]. |
| Key Risk Indicators (KRIs) | Metric | Quantifiable measures (e.g., query aging, screening failure rate) that act as early warning signals for emerging operational and data quality risks [34]. |
| Quality Tolerance Limits (QTLs) | Metric | Predefined study-level thresholds for critical data and processes (e.g., rate of primary endpoint misclassification) that signal a potential threat to trial integrity [30] [34]. |
Advanced Methodologies: Detailed Experimental Protocols for Key RBQM Components
Protocol for Developing and Implementing Key Risk Indicators (KRIs)
Objective: To proactively identify and monitor operational and data quality risks through specific, measurable, and actionable indicators.
Materials: Clinical trial protocol, RBQM plan, EDC and CTMS systems, data visualization or RBQM software.
Methodology:
- KRI Identification: Based on the pre-study risk assessment, define 5-10 core KRIs that are strong predictors of the prioritized risks. Common KRIs in Clinical Data Management include [34]:
- Data Entry Timeliness: Days between patient visit and data entry into EDC.
- Query Rate: Number of data queries raised per data point or per site.
- Protocol Deviation Rate: Frequency and severity of deviations from the protocol.
- Missing Data Proportion: Percentage of missing values in critical data fields.
- KRI Specification: Ensure each KRI is Specific, Measurable, Actionable, Relevant, and Timely (SMART) [34]. For example: "The percentage of case report form pages not entered within 3 days of a patient's visit must be below 10% for each site."
- Automation and Integration: Configure systems to automatically extract data from EDC and CTMS to calculate KRIs. Implement automated alerts in the RBQM platform to notify the study team when a KRI threshold is breached [34].
- Review and Action: Integrate KRI review into regular cross-functional team meetings. When a KRI alert is triggered, the team must determine the root cause and implement a targeted action, such as contacting the site for retraining or triggering a targeted on-site visit [34].
Protocol for Centralized Statistical Monitoring
Objective: To safeguard data integrity by identifying patterns of anomalous data, potential miscoding, or systematic errors across sites using statistical methods.
Materials: De-identified, accumulating clinical trial data from all sites, statistical software (e.g., R, SAS) or a specialized RBQM platform with statistical capabilities.
Methodology:
- Data Preparation: Extract a standardized dataset from the EDC at regular intervals (e.g., weekly). Key variables include site ID, patient ID, demographic data, primary/secondary endpoint data, and key safety data.
- Statistical Analysis Plan for Centralized Monitoring: Pre-specify the analytical methods, which may include:
- Site Comparison Analysis: Use descriptive statistics and graphical methods (e.g., box plots, scatter plots) to compare the distribution of key continuous variables (e.g., blood pressure, lab values) across all sites. Flag sites with distributions that are significantly different from the overall pool [30].
- Digit Preference and Benford's Law Analysis: Test for unusual patterns in digit distribution for numerical data, which can suggest data fabrication or poor quality recording [30].
- Endpoint Anomaly Detection: For the primary endpoint, use statistical models to identify outliers or unexpected patterns of response that cluster at a specific site [30].
- Output and Interpretation: The RBQM platform or statistician generates a report highlighting sites and variables with potential anomalies. The cross-functional team reviews these findings not as proof of error, but as a hypothesis-generating tool to guide targeted follow-up.
- Targeted Action: Findings from statistical monitoring are used to trigger specific actions, such as increased source data review for specific patients at a flagged site, clarification with the investigator, or a targeted audit [30] [31].
The evolution from rigid, monitoring-centric oversight to a dynamic, quality-focused RBQM framework is a cornerstone of modern clinical research. By integrating the principles of risk-based surveillance—targeting, adaptation, and value of information—RBQM allows sponsors to concentrate resources on the factors most critical to a trial's success. As the industry gains experience with ICH E6 (R2) and prepares for ICH E6 (R3), the adoption of advanced methodologies like AI-driven risk detection and real-time data analytics will further enhance the precision and efficiency of clinical trial oversight [30] [35]. The ultimate goal is a learning system where insights from one trial continuously refine the risk-based surveillance strategies of the next, ensuring that clinical development becomes progressively more ethical, efficient, and capable of delivering reliable evidence for healthcare decision-making.
The dynamic evaluation of safety risks throughout all stages of clinical development has become standard practice in modern pharmacovigilance [37]. In early clinical phases, where safety data for novel compounds is inherently limited, the need for practical tools that enable proactive risk assessment is particularly critical. Visual safety risk matrices have emerged as instrumental tools for addressing this need, providing multidisciplinary teams with intuitive, visual snapshots of projected safety risk profiles [37] [38]. These matrices facilitate clearer communication among the multiple stakeholders involved in early development decisions, from clinical scientists and safety assessors to regulatory affairs professionals and project managers.
Framed within the broader context of risk-based surveillance strategies for early detection research, visual risk matrices represent a paradigm shift from reactive to proactive safety assessment [8] [9]. The fundamental principle underpinning these tools is the systematic organization of risks based on their probability of occurrence and potential impact on patient safety or trial integrity. This approach allows clinical teams to prioritize risks objectively and implement targeted mitigation strategies before issues escalate, thereby potentially reducing the likelihood of costly late-stage development failures or post-market safety events.
Theoretical Foundation and Design Principles
Core Components of Visual Safety Risk Matrices
The architecture of an effective visual safety risk matrix rests on two fundamental dimensions: probability (likelihood) and impact (severity) [39] [40]. These orthogonal dimensions create a grid-based visualization that enables systematic risk categorization and prioritization. In early clinical development, probability refers to the estimated frequency with which a specific safety event might occur, while impact denotes the potential consequences on patient health, trial integrity, or program viability should the event materialize.
The 5x5 risk matrix configuration has gained particular prominence in clinical settings due to its superior granularity compared to simpler 3x3 alternatives [39]. This configuration utilizes five distinct categories for both probability and impact, creating a 25-cell matrix that provides sufficient discrimination for meaningful risk prioritization without overwhelming complexity. The probability axis typically ranges from "Rare" (unlikely to occur) to "Almost Certain" (sure to happen), while the impact axis spans from "Insignificant" (minimal consequences) to "Severe" (potentially life-threatening or trial-terminating consequences) [39]. Each cell within this matrix corresponds to a specific risk level, enabling clinical teams to quickly identify which safety concerns warrant immediate attention versus those that can be monitored with standard surveillance.
Visual Design and Standardization
Effective visual communication relies heavily on standardized color-coding systems that trigger instinctive recognition [41]. In safety risk matrices, this typically follows the convention of red for high-risk areas requiring immediate action, yellow/amber for moderate risks needing timely review, and green for lower-priority risks where existing controls are considered adequate [39] [41]. This color scheme aligns with regulatory frameworks such as ANSI Z535 and ISO 3864, which standardize safety colors to ensure consistent interpretation across different contexts and geographic regions [41].
The strategic application of color transforms abstract risk data into an intuitive visual landscape where the most critical threats immediately draw attention. This visual immediacy is particularly valuable in early clinical development, where multidisciplinary teams must rapidly assimilate complex safety information during protocol development, data monitoring, and strategic decision-making meetings. The matrix serves not only as an assessment tool but also as a communication platform that bridges knowledge gaps between team members with diverse expertise.
Application Protocol: Implementing Visual Risk Matrices in Early Clinical Trials
Risk Identification and Assessment Workflow
The implementation of visual risk matrices follows a structured workflow that begins with comprehensive risk identification and proceeds through systematic assessment, mitigation planning, and ongoing monitoring. The following diagram illustrates this iterative process:
Diagram 1: Risk assessment workflow
Step 1: Risk Identification - Conduct systematic brainstorming sessions with key stakeholders including clinical scientists, pharmacologists, toxicologists, biostatisticians, and regulatory affairs specialists [40]. Utilize techniques such as literature review, preclinical data analysis, analogous compound assessment, and expert consultation to generate a comprehensive list of potential safety risks [42]. Document each identified risk using standardized terminology that clearly describes the nature of the concern, potential triggering mechanisms, and relevant background context.
Step 2: Probability Assessment - Evaluate the likelihood of each identified risk occurring during the early clinical trial phase. Base assessments on available preclinical data, pharmacological properties of the compound, known class effects, and relevant patient population factors. Use the standardized probability categories outlined in Table 1 to ensure consistent rating across different risk types and assessors.
Step 3: Impact Evaluation - Assess the potential consequences should each risk materialize, considering multiple dimensions including patient safety, trial integrity, data interpretability, regulatory implications, and program timelines. Apply the impact categories detailed in Table 1, ensuring that ratings reflect the worst plausible outcome given the early clinical context and available risk controls.
Step 4: Risk Level Calculation - Compute the initial risk level for each item by multiplying the probability and impact scores, then position them on the visual matrix according to their calculated values. This creates the foundational risk landscape that will guide subsequent mitigation efforts and resource allocation.
Risk Prioritization and Matrix Visualization
Once risks have been assessed and positioned on the matrix, the visual representation enables immediate prioritization. The following table presents the standardized scoring system used for quantitative risk assessment in early clinical development:
Table 1: 5x5 Risk Matrix Scoring Criteria for Early Clinical Development
| Probability | Numeric Score | Impact | Numeric Score | Risk Level | Color Code | Required Action |
|---|---|---|---|---|---|---|
| Rare | 1 | Insignificant | 1 | 1-4: Acceptable | Green | Maintain current controls; no additional action required |
| Unlikely | 2 | Minor | 2 | 5-9: Adequate | Light Green | Consider for further analysis during routine monitoring |
| Moderate | 3 | Significant | 3 | 10-16: Tolerable | Yellow | Review in timely manner; implement improvement strategies |
| Likely | 4 | Major | 4 | 17-25: Unacceptable | Red | Immediate action required; may necessitate protocol amendment |
| Almost Certain | 5 | Severe | 5 |
The resulting matrix provides an instantaneous visual summary of the risk landscape, with color-coding enabling rapid identification of priority areas. This visualization is particularly valuable during multidisciplinary safety review meetings, where it focuses discussion on the most consequential risks and facilitates consensus on appropriate mitigation strategies [37]. The matrix serves as both an assessment tool and communication device, ensuring all stakeholders share a common understanding of the relative importance of different safety concerns.
Risk Mitigation and Monitoring Protocols
For risks categorized in the "Tolerable" (yellow) and "Unacceptable" (red) zones, develop specific mitigation plans that detail the actions required to reduce either the probability of occurrence, the severity of impact, or both. Assign clear ownership for each mitigation action, establish realistic timelines for implementation, and define specific metrics for evaluating effectiveness. Common mitigation strategies in early clinical development include additional safety monitoring, protocol-specified dose adjustments, revised eligibility criteria, implementation of independent data monitoring committees, and targeted training for investigational site staff.
Implement a continuous monitoring process that tracks both the status of identified risks and the effectiveness of mitigation measures. Schedule regular formal reviews of the risk matrix—typically at predetermined milestones such as completion of cohort enrollment, safety review meetings, or protocol amendments—to reassess existing risks and identify any new concerns that may have emerged. The dynamic nature of early clinical development necessitates this iterative approach to risk management, as accumulating data may alter the perceived probability or impact of previously identified safety concerns [37].
Integration with Risk-Based Surveillance Strategies
Visual safety risk matrices function as a core component within comprehensive risk-based surveillance frameworks for early detection research [8] [9]. This integration enhances the efficiency and effectiveness of safety monitoring by focusing resources on the highest-priority concerns while maintaining appropriate vigilance across the entire risk spectrum. The conceptual relationship between risk assessment and surveillance strategies is illustrated below:
Diagram 2: Risk-based surveillance cycle
The optimization of surveillance resources represents a critical application of visual risk matrices in early clinical development. Rather than applying uniform monitoring intensity across all potential safety concerns, risk-based surveillance strategically allocates resources according to the priorities established through the matrix assessment [8] [9]. This approach recognizes that focusing solely on the highest-risk areas may not always be optimal; instead, a balanced surveillance strategy that considers spatial correlation in risk and available detection methodologies often yields superior detection capability [8].
In practice, this means designing monitoring plans that implement intensified surveillance for risks positioned in the "Unacceptable" (red) zone of the matrix, standard monitoring for "Tolerable" (yellow) risks, and routine surveillance for lower-priority concerns. This resource allocation strategy enhances the probability of early detection while maintaining operational efficiency—a critical consideration in early clinical development where monitoring resources are often constrained [8] [29]. The resulting surveillance plan becomes a dynamic component of the overall risk management strategy, evolving as new safety information emerges and risks are re-categorized based on accumulating clinical data.
Experimental Protocols and Methodologies
Protocol 1: Matrix Customization for Specific Research Areas
Purpose: To tailor the generic visual risk matrix framework to address the specific safety assessment needs of a particular drug class, therapeutic area, or trial design.
Materials and Equipment:
- Preclinical data package (pharmacology, toxicology, DMPK)
- Relevant scientific literature on compound class and therapeutic area
- Regulatory guidelines relevant to the drug class and indication
- Multidisciplinary team representation (clinical science, toxicology, pharmacology, regulatory, biostatistics)
- Digital template of standardized risk matrix
Procedure:
- Therapeutic Context Analysis: Review the specific mechanism of action, preclinical findings, and known class effects to identify safety concerns particular to the drug class and intended patient population.
- Probability Calibration: Adapt the generic probability categories to reflect the specific context. For example, for a compound with hepatotoxic potential, define "Rare" as <1% incidence, "Unlikely" as 1-5%, "Moderate" as 5-10%, "Likely" as 10-20%, and "Almost Certain" as >20% based on preclinical signals and class information.
- Impact Criteria Specification: Customize impact definitions to address therapeutic context. In oncology trials, for example, certain severe adverse events might be categorized differently than in chronic non-life-threatening conditions.
- Matrix Validation: Present draft customized matrix to independent subject matter experts for review and refinement before implementation.
Validation: Assess inter-rater reliability among team members applying the customized matrix to standardized case scenarios. Refine definitions and criteria until acceptable consistency (≥80% agreement) is achieved.
Protocol 2: Prospective Risk Assessment for FIH Trial Design
Purpose: To systematically identify and evaluate potential safety risks during the design phase of a First-In-Human (FIH) clinical trial to inform protocol development and risk management planning.
Materials and Equipment:
- Complete preclinical data package
- Draft clinical trial protocol
- Preliminary investigator brochure
- Visual risk matrix software or template
- Regulatory guidelines for FIH trials
Procedure:
- Starting Dose Justification Review: Evaluate the adequacy of the proposed starting dose based on all relevant nonclinical data (NOAEL, MABEL, or other appropriate metrics).
- Dose Escalation Scheme Assessment: Examine the proposed dose escalation scheme for potential risks, including the size of increment between dose levels, duration of observation periods, and criteria for progression.
- Safety Monitoring Evaluation: Assess the adequacy of proposed safety monitoring measures, including the frequency and type of assessments, stopping rules, and criteria for dose escalation.
- Patient Population Considerations: Evaluate inclusion/exclusion criteria for their effectiveness in mitigating specific risks identified from preclinical data.
- Risk-Benefit Integration: Position all identified risks on the visual matrix and review the overall risk-benefit balance of the proposed trial design.
Output: A comprehensive risk assessment that informs final protocol development, including specific recommendations for risk mitigation strategies and safety monitoring intensification in areas of highest concern.
Protocol 3: Dynamic Risk Reassessment During Trial Conduct
Purpose: To establish a systematic process for updating the visual risk matrix based on emerging clinical data during trial conduct.
Materials and Equipment:
- Initial risk assessment matrix
- Accumulating clinical trial data (safety, pharmacokinetic, pharmacodynamic)
- Data visualization tools
- Updated literature relevant to the compound class
Procedure:
- Define Reassessment Triggers: Establish predetermined triggers for risk reassessment (e.g., completion of each cohort, occurrence of specific adverse events, emergence of new external information).
- Data Collation: Collect and organize all relevant new data since the last assessment, including safety reports, laboratory abnormalities, pharmacokinetic findings, and any other observations.
- Probability Re-evaluation: Adjust probability estimates based on observed incidence rates and emerging patterns.
- Impact Re-evaluation: Reassess potential impact in light of observed event severity and clinical management requirements.
- Matrix Repositioning: Update the positions of risks on the visual matrix to reflect the revised assessments.
- Mitigation Strategy Adjustment: Modify risk mitigation plans based on the updated matrix, intensifying or reducing measures as appropriate.
Frequency: Conduct scheduled reassessments at predefined milestones, with provision for unscheduled reassessment if significant new safety information emerges.
Research Reagent Solutions
Table 2: Essential Research Reagents and Tools for Visual Risk Assessment Implementation
| Tool/Reagent | Function | Application Notes |
|---|---|---|
| Standardized Matrix Template | Provides consistent framework for risk assessment | Customize for specific therapeutic areas; ensure regulatory alignment |
| Safety Database Interface | Facilitates real-time safety data integration | Should accommodate both structured and unstructured data sources |
| Color-Coding System | Enables visual risk prioritization | Adhere to ANSI Z535/ISO 3864 standards for universal recognition [41] |
| Risk Assessment Software | Supports dynamic risk tracking and visualization | Select platforms with audit trail capabilities for compliance |
| Decision Rule Algorithms | Objectifies risk scoring and categorization | Predefine algorithms for consistency; allow expert override provisions |
| Data Visualization Tools | Transforms risk data into intuitive graphics | Ensure accessibility for all stakeholders, including color-blind users |
| Literature Surveillance System | Captures emerging external safety information | Implement automated alerts for relevant compound class safety issues |
Visual safety risk matrices represent a significant advancement in the proactive assessment and communication of safety risks during early clinical development. By transforming complex safety data into intuitive visual formats, these tools enhance multidisciplinary collaboration, support targeted resource allocation, and ultimately strengthen the risk-based surveillance strategies essential for early detection of potential safety concerns. The structured protocols and methodologies outlined in this document provide a framework for implementation that can be adapted to specific research contexts while maintaining alignment with regulatory expectations and industry best practices. As risk-based approaches continue to evolve in clinical development, visual risk matrices will likely play an increasingly central role in ensuring that safety assessment remains both scientifically rigorous and operationally practical throughout the drug development lifecycle.
Grid-based surveillance represents an advanced methodology for monitoring high-risk and mobile populations in public health, particularly for infectious disease control. This approach, which leverages grassroots-level community governance structures, enables precise targeting and continuous monitoring of populations that are typically difficult to reach through conventional health systems. Originally developed during the 2003 SARS crisis in China, grid-based surveillance has since been refined and successfully implemented in various contexts, most notably in China's malaria elimination program and along high-risk border regions. This protocol details the application, implementation mechanisms, and operational procedures of grid-based surveillance systems, providing researchers and public health professionals with a framework for adapting this model to diverse epidemiological contexts.
Grid-based surveillance is a grassroots governance strategy that reallocates administrative resources at a neighborhood level to improve governmental efficiency in actively identifying and solving problems among populated regions [43]. The system originated from the 2003 SARS crisis in China and has been maintained by the Chinese government as a mechanism for addressing social crises [43]. The term "grid" refers to the lowest level of urban governance below urban communities, typically covering a small geographic area of roughly 10 km² [43].
In public health applications, this approach has demonstrated particular effectiveness in monitoring mobile and migrant populations (MMPs) in high-risk border regions, playing an indispensable role in promoting and consolidating disease elimination efforts by tracking and timely identification of potential disease importation or re-establishment [43]. The system's value became particularly prominent during the COVID-19 pandemic, where it contributed to virus containment at the neighborhood level through functions including routine body temperature checks, travel history verification, transfer of infected residents to designated hospitals, and monitoring of quarantined households [43].
Conceptual Framework and Key Principles
The theoretical foundation of grid-based surveillance rests on several core principles that differentiate it from conventional surveillance approaches:
Spatial Segmentation
The grid system divides larger administrative units into smaller, manageable geographic segments, allowing for more precise monitoring and resource allocation. This segmentation enables targeted interventions specific to each grid's unique characteristics and risk profile.
Multi-sectoral Integration
Grid-based surveillance operates through coordinated action across multiple sectors under governmental guidance, including health facilities, residents, families, and communities that actively participate in surveillance activities [43]. This integration facilitates comprehensive population coverage.
Adaptive Resource Allocation
Unlike static surveillance systems, grid-based approaches allow dynamic reallocation of resources based on real-time risk assessment. This principle acknowledges that spatial correlation in risk can make it suboptimal to focus solely on the highest-risk sites, necessitating a balanced approach to resource distribution [8].
Proximity-based Monitoring
By leveraging community members as grid administrators, the system capitalizes on local knowledge and social networks to identify and monitor high-risk individuals who might otherwise evade traditional surveillance mechanisms.
Table 1: Core Principles of Grid-Based Surveillance
| Principle | Description | Implementation Benefit |
|---|---|---|
| Spatial Segmentation | Dividing large areas into manageable geographic units | Enables precise targeting of interventions |
| Multi-sectoral Integration | Coordinating across health, administrative, and community sectors | Provides comprehensive population coverage |
| Adaptive Resource Allocation | Dynamically distributing resources based on real-time risk | Optimizes use of limited surveillance resources |
| Proximity-based Monitoring | Utilizing local community members as monitors | Enhances detection of hard-to-reach populations |
Operational Mechanism and Infrastructure
The operational structure of grid-based surveillance follows a vertical-horizontal combined framework that enables efficient information flow and response coordination.
Administrative Structure
Vertical Information Flow
In the vertical structure, information about mobile and migrant populations is reported through multiple administrative tiers [43]. The standard reporting pathway moves from:
- Village level → Township level → County level → Provincial level → National level
This vertical integration ensures that local data reaches national decision-making bodies while maintaining contextual information at each administrative level.
Horizontal Implementation Structure
The horizontal structure is characterized by grid-based strategy implementation across communities [43]. This component supports both annual national MMPs surveys and day-to-day MMPs surveillance through localized implementation networks.
Key Personnel and Roles
The system relies on three primary roles within each grid unit:
Grid Administrator: Selected by or volunteered from the local community, this individual leads community groups and collects necessary information (e.g., travel plans/history) on MMPs within the community [43].
Village Committee Staff: Provide official administrative support and coordination with broader governmental structures.
Village Doctor: Delivers medical expertise, conducts preliminary assessments, and facilitates connections to the formal healthcare system.
Case Study: Grid-Based Malaria Surveillance in China-Myanmar Border Region
China's successful malaria elimination program, which achieved WHO-certified malaria-free status in June 2021, provides a compelling case study for grid-based surveillance implementation [44]. After recording 30 million annual cases in the 1940s, China reduced malaria cases to zero indigenous cases by 2016 through a decades-long, multi-pronged effort that incorporated grid-based approaches in high-risk regions [44].
Implementation Context
Yunnan Province, located in southwestern China, presented particular challenges for malaria control, sharing a 4,060 km long porous, natural, barrierless border with malaria-endemic countries including Myanmar, Laos, and Vietnam [43]. This region accounted for approximately 30% of the nearly 3,000 imported malaria cases reported annually in China, with 97.2% of cases in Yunnan Province classified as imported between 2014-2019 [43].
The China-Myanmar border region represented one of the highest-risk areas for malaria re-establishment due to:
- Frequent population movement across informal border-crossing points
- Continuous importation of malaria infections
- Wide distribution of efficient mosquito vectors
- Limited access to health services in marginalized regions
Surveillance Framework
The grid-based surveillance system implemented in Tengchong County, at the westernmost edge of Yunnan Province, employed a structured approach to malaria monitoring:
Table 2: Grid-Based Malaria Surveillance Outcomes in Tengchong County (2013-2020)
| Surveillance Component | Pre-Implementation (2013-2015) | Post-Implementation (2016-2020) | Improvement |
|---|---|---|---|
| Case Reporting Timeliness | 5-7 days | ≤1 day | 80% reduction |
| Case Investigation Completion | 7-10 days | ≤3 days | 70% reduction |
| Foci Response Initiation | 10-14 days | ≤7 days | 50% reduction |
| MMP Coverage | ~65% | ~92% | 42% increase |
| High-Risk Village Screening | 45% | 88% | 96% increase |
The "1-3-7" Approach Integration
Grid-based surveillance operated in conjunction with China's "1-3-7" surveillance strategy, which mandated [44]:
- 1 day: Case reporting after detection
- 3 days: Case investigation and confirmation
- 7 days: Implementation of appropriate foci response measures
This approach was specifically aimed at interrupting indigenous transmission and led to four consecutive years of zero indigenous cases, enabling China to apply for WHO certification in 2020 [44].
Protocol: Implementation of Grid-Based Surveillance
Pre-Implementation Assessment
Geographic Segmentation Protocol
- Define Implementation Area: Delineate the total geographic region requiring surveillance.
- Identify Population Density Clusters: Map residential clusters, commercial areas, and transit points.
- Establish Grid Boundaries: Divide the area into manageable grid units of approximately 10 km² each, adjusting for population density and geographic barriers.
- Characterize Grid-Specific Risks: Assess each grid for population mobility patterns, existing disease burden, and environmental risk factors.
Resource Mapping
- Identify Existing Health Infrastructure: Map health facilities, diagnostic capacity, and treatment resources within each grid.
- Inventory Human Resources: Identify potential grid administrators, community health workers, and volunteers.
- Assess Communication Infrastructure: Evaluate mobile network coverage, internet access, and transportation networks.
Personnel Training Protocol
Grid Administrator Training Curriculum
- Module 1: Surveillance Objectives and Case Definitions (4 hours)
- Recognizing target diseases and conditions
- Understanding reporting criteria and thresholds
- Module 2: Data Collection Methods (6 hours)
- Administering standardized questionnaires
- Recording travel histories and risk exposures
- Module 3: Community Engagement Techniques (4 hours)
- Building trust with mobile populations
- Cultural sensitivity and communication strategies
- Module 4: Referral Procedures (2 hours)
- Connecting individuals to health services
- Emergency response protocols
Data Collection and Reporting Workflow
The grid-based surveillance system operates through a structured data collection and reporting workflow that ensures timely information flow from community to national levels while maintaining data quality and enabling rapid response.
Quality Assurance Protocol
Data Verification Procedures
- Random Spot Checks: 10% of reported data undergoes independent verification monthly.
- Cross-Validation: Compare grid-collected data with health facility records.
- Completeness Audits: Weekly assessment of reporting compliance across all grids.
Performance Metrics
- Reporting timeliness (>95% within 24 hours)
- Data completeness (>90% of required fields)
- Case detection sensitivity (benchmarked against health facility data)
Research Reagent Solutions and Technical Tools
Successful implementation of grid-based surveillance requires specific technical tools and resources that enable efficient data collection, analysis, and response coordination.
Table 3: Essential Research Reagents and Technical Tools for Grid Surveillance
| Tool Category | Specific Solution | Function | Implementation Example |
|---|---|---|---|
| Data Collection Tools | Mobile Data Capture Apps | Enables real-time field data entry | Customized forms for symptom reporting and travel history |
| Geographic Information Systems | Grid Mapping Software | Supports spatial analysis and risk mapping | ArcGIS or QGIS for grid boundary definition and hotspot identification |
| Laboratory Diagnostics | Rapid Diagnostic Tests (RDTs) | Provides point-of-care testing capability | Malaria RDTs used by village doctors in border regions |
| Data Analysis Platforms | Statistical Software (R, Python) | Facilitates epidemiological analysis and modeling | R package for geostatistical analysis of surveillance data |
| Communication Systems | Mobile Messaging Platforms | Enables rapid alert dissemination | SMS-based alert system for grid administrators |
| Database Management | Real-time Surveillance Databases | Centralizes data storage and access | China's Migrant Population Service Center (MPSC) database |
Adaptation and Scaling Considerations
Contextual Adaptation Framework
Grid-based surveillance requires customization based on local epidemiological, demographic, and infrastructural factors:
High-Resource Settings
- Enhanced electronic health record integration
- Automated risk algorithm development
- Digital mobility data incorporation
Limited-Resource Settings
- Paper-based data collection with periodic digitization
- Community health worker-focused implementation
- Mobile technology optimization where available
Evaluation Metrics for Program Effectiveness
Comprehensive evaluation of grid-based surveillance systems should incorporate both process and outcome measures:
Table 4: Grid Surveillance Performance Evaluation Framework
| Evaluation Domain | Key Performance Indicators | Measurement Frequency | Target Threshold |
|---|---|---|---|
| System Sensitivity | Proportion of true cases detected | Quarterly | >90% in high-risk grids |
| Timeliness | Average time from case identification to report | Weekly | <24 hours |
| Population Coverage | Proportion of target population enrolled | Monthly | >85% in priority grids |
| Data Quality | Completeness and accuracy of key variables | Monthly | >90% completeness |
| Cost Efficiency | Cost per case detected | Annually | Context-specific benchmarks |
| Impact | Reduction in transmission indicators | Annually | Statistical significance |
Grid-based surveillance represents a robust methodology for monitoring high-risk populations that complements traditional health system-based surveillance. Its effectiveness stems from the integration of community-level intelligence with formal health reporting structures, creating a comprehensive system particularly suited to detecting imported cases and preventing re-establishment of disease transmission in elimination settings.
The successful application of this approach in China's malaria elimination program, particularly along the high-risk China-Myanmar border, demonstrates its potential for adaptation to other contexts and public health priorities. Future implementations should incorporate rigorous evaluation frameworks to further refine the model and establish evidence-based best practices for grid-based surveillance across diverse epidemiological contexts.
Leveraging Centralized Data and Real-Time Analytics for Proactive Oversight
The following tables summarize key quantitative data points and performance benchmarks essential for implementing a proactive oversight system.
Table 1: Key Performance Indicators (KPIs) for Centralized Monitoring Systems
| KPI Category | Specific Metric | Target Benchmark | Data Source |
|---|---|---|---|
| Data Quality | Rate of protocol deviations | Industry benchmark required | Electronic Data Capture (EDC), Risk Assessment Platforms [45] |
| Site Performance | Patient enrollment rate | Industry benchmark required | Clinical Trial Management System (CTMS), Historical Data [45] |
| Patient Safety | Incidence of adverse events | Industry benchmark required | Safety Databases, Electronic Health Records (EHR) [45] |
| Process Efficiency | Data entry lag time (days) | Industry benchmark required | EDC Metadata, Audit Trails [45] |
Table 2: Real-Time Analytics Performance Benchmarks
| Performance Metric | Optimal Value | Importance for Proactive Oversight |
|---|---|---|
| Response Time for Automated Alerts [46] | ≤ 100 milliseconds | Enables immediate action in high-risk scenarios (e.g., patient safety, fraud). |
| Data Latency for Dashboards [46] | 25 - 50 milliseconds | Ensures decision-makers access the most current data for oversight. |
| AI Model Performance (e.g., STARHE-RISK) [47] | Accuracy: 0.72 (95% CI 0.57–0.84) | Provides reliable, automated risk stratification for early issue detection. |
Experimental Protocols for Risk-Based Surveillance
Protocol for AI-Driven Risk Stratification in Disease Surveillance
This protocol outlines the methodology for developing a deep learning model to stratify patients based on disease risk, as demonstrated in hepatocellular carcinoma (HCC) detection research [47].
Objective: To design an ultrasound-based deep learning model for disease risk stratification and early detection in a patient cohort. Materials:
- Prospective, multicentric study population (e.g., n=403 patients) [47].
- Ultrasound cine clips (e.g., of liver parenchyma and any tumors).
- Associated clinical and blood parameter data.
- High-performance computing infrastructure with GPU support.
Methodology:
- Patient Cohort Definition: Define inclusion/exclusion criteria (e.g., adults with a specific condition, enrolled in a surveillance program for a minimum period, with no prior history of the target disease).
- Data Acquisition: Acquire standardized ultrasound cine clips from two groups:
- Cases: Patients who developed the target disease (e.g., n=152 with early-stage HCC).
- Controls: Patients without the disease at inclusion and during a subsequent follow-up period (e.g., 1 year; n=170).
- Data Preprocessing & Partitioning:
- Stratify the dataset into training/validation and independent testing sets based on potential confounders.
- Allocate patients to the independent testing set based on sample size calculation (e.g., n=50, balanced between groups).
- Model Training:
- Risk Stratification Model (e.g., STARHE-RISK): Train a deep learning model (e.g., Convolutional Neural Network) on cine clips of non-diseased tissue from cases and controls.
- Detection Model (e.g., STARHE-DETECT): Train a separate model on cine clips containing confirmed diseased tissue.
- Model Validation & Integration:
- Evaluate model performance on the independent test set using metrics like accuracy, sensitivity, specificity, and odds ratio.
- Integrate the model's prediction with complementary clinical and blood-based scores to enhance specificity and overall performance.
Protocol for Real-Time Centralized Monitoring in Clinical Trials
This protocol describes the implementation of a centralized, risk-based monitoring system for clinical trial oversight [45] [46].
Objective: To establish a continuous, data-driven monitoring system that shifts focus from extensive on-site source data verification (SDV) to centralized, risk-based oversight. Materials:
- Unified data platform (e.g., Cloud Data Warehouse) integrating EDC, CTMS, and other data sources [45] [46].
- Real-time data pipelines (e.g., using stream processing frameworks like Apache Kafka or Flink) [46].
- Pre-defined Critical-to-Quality (CTQ) factors, Key Risk Indicators (KRIs), and Quality Tolerance Limits (QTLs) [45].
Methodology:
- System Setup:
- Digitize Protocol: Create a digital protocol to automatically identify CTQ factors and populate downstream systems (EDC, risk platforms) [45].
- Define Risk Indicators: Establish a set of KRIs and QTLs for data quality, patient safety, and site performance.
- Integrate Data Feeds: Use real-time data pipelines to stream operational data from EDC, CTMS, and other sources into a centralized cloud data warehouse [46].
- Real-Time Surveillance:
- Automated Signal Detection: Implement AI and automation to continuously analyze incoming data against KRIs and QTLs, generating real-time alerts for anomalies [45].
- Leverage Generative AI: Use GenAI to process audit data in real-time to identify site compliance variability or potential misconduct [45].
- Dynamic Response:
- Central Monitoring Workflow: Central monitors review AI-generated alerts and triggers.
- Issue Management: Log and track all identified issues in an integrated system.
- Targeted On-site Monitoring: Use insights from central monitoring to plan targeted on-site visits, focusing on source data review (SDR) and process improvement instead of extensive SDV [45].
Signaling Pathways and Workflow Visualizations
Centralized Monitoring Ecosystem
AI-Driven Risk Stratification Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table 4: Essential Materials and Tools for Advanced Research Surveillance
| Item / Solution | Function / Application |
|---|---|
| Unified Data Platform | Centralizes disparate data sources (EDC, CTMS, EHR) for holistic oversight and streamlined processes [45]. |
| Real-Time Data Pipeline (e.g., Apache Kafka) | Enables continuous ingestion and processing of high-velocity data streams from various sources for immediate analysis [46]. |
| Cloud Data Warehouse (e.g., Snowflake) | Provides scalable, elastic storage and immense computing power required for real-time data analysis [46]. |
| Stream Processing Framework (e.g., Apache Flink) | Facilitates instant data transformation and analysis upon arrival, enabling true real-time analytics [46]. |
| AI/ML Models for Predictive Analytics | Analyzes live data streams for predictive maintenance, anomaly detection, and risk stratification [45] [46] [47]. |
| Digital Protocol | Serves as a central, accurate source of information, automating the population of downstream systems and reducing manual error [45]. |
Navigating Implementation Hurdles and Strategic Optimizations
Addressing Resource and Infrastructure Limitations in Diverse Settings
Resource and infrastructure limitations present significant challenges across various sectors, including healthcare, agricultural security, and public health. Effectively addressing these constraints is crucial for implementing robust risk-based surveillance strategies for early detection of threats, from infectious diseases in human populations to emerging pathogens in agricultural systems. This article provides application notes and detailed protocols for designing and implementing effective surveillance and response mechanisms in diverse, resource-constrained environments. By integrating strategic planning with optimized resource allocation, these protocols enable researchers, scientists, and drug development professionals to enhance early detection capabilities despite infrastructural limitations, ultimately supporting more resilient systems in settings where traditional resource-intensive approaches are not feasible.
Defining Resource-Constrained Settings
In the context of surveillance and early detection research, a resource-poor or constrained setting is defined as a locale where the capability to conduct comprehensive monitoring and response is limited to basic tools and personnel [48]. This may be stratified into three categories:
- No resources: Settings lacking even fundamental surveillance capabilities.
- Limited resources: Settings with basic surveillance tools but limited capacity for expansion.
- Limited resources with possible referral: Settings with basic capabilities and potential access to higher-level support systems.
For surveillance operations, this encompasses activities across the entire spectrum, from community-based monitoring and field data collection to laboratory analysis and centralized reporting, without regard to the specific location where these activities occur [48].
Quantitative Assessment of Infrastructure Limitations
Understanding the current global landscape of infrastructure access is crucial for designing appropriate surveillance strategies. The data reveals significant disparities that directly impact implementation capabilities.
Table 1: Global Infrastructure Access and Inequality Metrics (2020)
| Infrastructure Type | Global North Mean Access | Global South Mean Access | Access Ratio (North:South) | Inequality Level (Global South) |
|---|---|---|---|---|
| Economic | 0.49 | 0.39 | 1.25:1 | 9-44% higher |
| Social | 0.39 | 0.29 | 2.00:1 | 9-44% higher |
| Environmental | 0.42 | 0.35 | 1.43:1 | 9-44% higher |
Source: Adapted from Nature Human Behaviour (2025) [49]
The data demonstrates that Global South countries experience only 50-80% of the infrastructure access of Global North countries, while their associated inequality levels are 9-44% higher [49]. These disparities directly impact the implementation of surveillance systems, particularly in areas requiring specialized equipment, stable energy supplies, or advanced transportation networks for sample collection and analysis.
Table 2: Infrastructure Access Classification by Country Type
| Classification Category | Representative Countries | Infrastructure Access Pattern |
|---|---|---|
| H-H-H (High access all categories) | Australia, Canada, Chile, Portugal | High economic, social, and environmental infrastructure |
| L-L-L (Low access all categories) | Burkina Faso, Chad, Niger, South Sudan | Limited infrastructure across all dimensions |
| H-H-L (High socio-economic, low environmental) | China, India | Strong economic and social infrastructure but constrained environmental access |
Source: Adapted from Nature Human Behaviour (2025) [49]
Risk-Based Surveillance Framework for Early Detection
Conceptual Framework for Optimized Surveillance
Effective surveillance in resource-constrained settings requires a strategic approach that optimizes limited resources while maximizing detection probability. The following framework illustrates the key components and their relationships:
Key Principles for Surveillance Optimization
Research demonstrates that conventional risk-based surveillance strategies often focus exclusively on the highest-risk sites, but this approach may be suboptimal. The optimal surveillance strategy depends on an interplay of factors including patterns of pathogen entry and spread, and the sensitivity of available detection methods [8]. Several key principles emerge from optimization modeling:
Spatial Correlation Consideration: When risk is spatially correlated, focusing solely on the highest-risk sites can be suboptimal. Distributing resources across multiple sites often yields better detection probability [8] [9].
Detection Method Interplay: The sensitivity of available detection methods directly influences optimal site arrangement. Higher sensitivity methods allow for more focused surveillance, while lower sensitivity methods require broader distribution [8].
Dynamic Resource Allocation: Fixed surveillance sites are less effective than adaptive strategies that account for changing risk patterns and introduction frequencies over time [9].
Experimental Protocols for Surveillance Implementation
Protocol 1: Strategic Surveillance Site Selection
Purpose: To identify optimal surveillance site arrangements that maximize detection probability while minimizing resource utilization.
Materials:
- Geographic Information System (GIS) software or mapping tools
- Host population distribution data
- Historical introduction risk data (if available)
- Transportation and access route maps
- Budget and resource constraints documentation
Procedure:
- Define Study Area: Delineate the geographic boundaries of the surveillance region and divide into 1km × 1km grid cells [8].
- Map Host Distribution: Document host density and distribution patterns across the grid using available census, agricultural, or satellite data [8] [9].
- Characterize Introduction Risk: Identify potential introduction pathways and quantify relative risk across the landscape based on:
- Proximity to transportation hubs
- Historical introduction data
- Trade and movement patterns
- Environmental suitability [8]
- Model Spread Dynamics: Parameterize secondary spread mechanisms using known dispersal kernels appropriate for the target pathogen or threat [9].
- Optimize Site Selection: Using computational optimization (e.g., simulated annealing), identify the arrangement of surveillance sites that maximizes probability of detection before a predefined prevalence threshold is reached [8].
- Validate and Adjust: Compare optimized site selection against conventional risk-based targeting and adjust based on practical field constraints.
Notes:
- The optimal arrangement is often counterintuitive - it may not include all the highest-risk sites [8].
- Consider spatial correlation of risk - when high-risk sites are clustered, spreading resources provides better coverage [9].
- Account for seasonal variations in risk patterns when establishing long-term surveillance.
Protocol 2: Integrated Capacity Building for Resource-Constrained Settings
Purpose: To strengthen fundamental infrastructure and capabilities that support surveillance activities in resource-constrained environments.
Materials:
- Assessment tools for current capabilities
- Stakeholder engagement framework
- Training materials adapted to local context
- Partnership development templates
- Monitoring and evaluation frameworks
Procedure:
- Baseline Assessment: Conduct comprehensive evaluation of existing infrastructure, including:
- Primary care and basic emergency response capabilities
- Transportation and communication systems
- Laboratory capacity and supply chains
- Trained personnel availability [48]
- Strengthen Primary Systems: Enhance foundational capabilities that support surveillance:
- Develop simple triage tools and protocols modifiable to resource limitations
- Train community health workers in recognition and initial response
- Establish referral pathways to higher-level care when available [48]
- Build Strategic Alliances: Establish formal relationships prior to emergency events with:
- Academic medical centers
- Professional societies
- Non-governmental organizations
- Governmental organizations [48]
- Develop Local Expertise: Implement training programs that:
- Leverage existing expertise across disciplines (surgery, obstetrics, internal medicine)
- Focus on preventative and supportive care to reduce critical needs
- Create innovative staffing methods to optimize limited human resources [48]
- Implement Progressive Enhancement: Focus limited resources at facilities where greatest benefit can be achieved, typically district or regional hospitals rather than primary clinics [48].
Notes:
- Capacity building should include education for families, community workers, and clinicians [48].
- Professional societies in resource-rich countries should advocate to mitigate intellectual "brain drain" from resource-poor countries [48].
- Performance improvement activities should be institutionalized to facilitate continuous learning [48].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Research and Surveillance Materials for Resource-Limited Settings
| Item/Category | Function/Application | Resource-Aware Considerations |
|---|---|---|
| Portable Diagnostic Kits | Field-based detection of pathogens or threats | Prioritize kits with long shelf lives, minimal refrigeration needs, and visual readouts |
| GIS and Spatial Mapping Tools | Identifying high-risk areas and optimizing site selection | Utilize open-source platforms; employ simplified mapping approaches when advanced GIS unavailable |
| Lateral Flow Assays | Rapid detection of specific biomarkers or pathogens | Select versions with minimal processing steps; prioritize cost-effectiveness for large-scale surveillance |
| Mobile Data Collection Platforms | Real-time data capture and transmission | Use basic mobile devices; implement offline capability with synchronization when connectivity available |
| Sample Transport Systems | Maintaining sample integrity from field to lab | Develop temperature-monitoring protocols using locally available cooling materials |
| Basic Laboratory Equipment | Essential processing and analysis capabilities | Focus on versatile, durable equipment with minimal maintenance requirements |
| Stakeholder Engagement Frameworks | Building collaborative networks across sectors | Adapt communication materials to local contexts and literacy levels |
Application in Huanglongbing (HLB) Case Study
The optimization approach for risk-based surveillance was applied to Huanglongbing (HLB) or citrus greening disease in Florida, providing a demonstrated case of its efficacy [8] [9]. The implementation followed these specific steps:
Model Parameterization: Created a spatially explicit model of HLB spread through commercial and residential citrus populations, using data on citrus density and psyllid vector dispersal [8].
Introduction Scenarios: Modeled multiple potential introduction scenarios accounting for uncertainty in entry timing and locations, particularly from human movements from infected areas [9].
Surveillance Optimization: Used stochastic optimization to identify surveillance site arrangements that maximized detection probability before the pathogen reached economically damaging prevalence levels [8].
Performance Comparison: Demonstrated that the optimized surveillance approach provided significant performance gains and cost savings compared to conventional risk-based methods [8] [9].
This case study confirmed that the optimal surveillance strategy for HLB did not simply target the highest-risk sites but distributed resources in a pattern that accounted for spatial correlation in risk and the sensitivity of available detection methods [9].
Addressing resource and infrastructure limitations in diverse settings requires a strategic approach that optimizes available resources while building sustainable capacity. The protocols and application notes presented here provide a framework for implementing effective risk-based surveillance strategies even in constrained environments. By integrating computational optimization with practical field implementation, and by building foundational capabilities through strategic partnerships, researchers and public health professionals can significantly enhance early detection capabilities for emerging threats. The case study on HLB surveillance demonstrates that these approaches yield tangible improvements in detection probability and cost efficiency compared to conventional methods. As infrastructure disparities persist globally, these resource-aware strategies become increasingly essential for effective global health security and agricultural protection.
Overcoming Data Standardization and Interoperability Gaps
Within modern public health and pharmaceutical research, risk-based surveillance strategies are critical for the early detection of emerging threats, from infectious diseases to drug safety signals [50]. The effectiveness of these strategies is fundamentally dependent on the seamless flow of high-quality data. However, data standardization and interoperability gaps present significant roadblocks, often causing critical delays in detection and analysis [51]. This document outlines the core challenges, provides structured protocols for implementing interoperable data systems, and offers a toolkit to enable researchers to overcome these barriers, thereby enhancing the sensitivity and timeliness of early detection research.
The Interoperability Landscape: Challenges and Quantitative Analysis
The drive towards health data interoperability is fueled by regulatory imperatives and the pressing need for connected care. By 2025, the adoption of standards like FHIR (Fast Healthcare Interoperability Resources) as a baseline for Electronic Health Record (EHR) vendors has grown significantly, pushed by mandates such as the 21st Century Cures Act in the US [52]. Despite this progress, persistent challenges stifle the data fluidity required for effective surveillance.
Core Interoperability Barriers
Research and implementation experiences reveal several consistent barriers:
- Legacy System Fragmentation: Many healthcare and research organizations, especially those using older EHR solutions, face vendor lock-in and isolated data silos. Integrating data across these disparate, proprietary systems is complex and costly [52] [51].
- Inconsistent Standards and Semantic Discord: Even with implemented standards like FHIR, HL7, or SNOMED CT, a lack of true semantic interoperability is common. Codes, units, and terms often differ between organizations, complicating data aggregation, analytics, and AI deployment [52]. The phenomenon of "Data Standards Fatigue"—the overwhelming feeling from the continuous introduction of new and overlapping standards—further exacerbates this issue [53].
- Regulatory and Compliance Complexity: Complying with a patchwork of evolving regulations (e.g., HIPAA, GDPR) and regional requirements (e.g., US FDA, EMA) introduces high-stakes complexity for data sharing across borders [52] [53].
- Workflow and Usability Deficits: Information inaccessibility and poor interoperability between care settings create inefficiencies for clinical researchers and can impact data quality and patient safety [52].
Quantitative Impact of Standardization Gaps
The table below summarizes key challenges and their documented impact on research and surveillance systems.
Table 1: Documented Challenges in Data Interoperability and Their Impacts
| Challenge Area | Specific Example | Documented Impact/Prevalence |
|---|---|---|
| Standards Proliferation | Overlap between ISO IDMP and FDA PQ/CMC standards [53] | Creates significant implementation challenges; requires substantial resources for mapping and harmonization. |
| Systemic Inconsistency | Use of multiple, conflicting standards in South African public hospitals [51] | Complicates data interoperability; noted lack of compliance with interoperability standards among hospitals. |
| Workflow Integration | Clinician frustration with EHR interoperability [52] | Causes inefficiencies and can potentially impact patient safety and data quality for research. |
| Workforce Skills | Lack of data standards expertise in the pharmaceutical industry [53] | A major obstacle to understanding and implementing complex data requirements effectively. |
Application Notes & Protocols for Enhanced Surveillance
To support the development of robust, risk-based surveillance systems, the following section provides detailed protocols and visual workflows.
Protocol 1: Implementing an Interoperable Data Pipeline for Surveillance
This protocol describes a methodology for establishing a centralized data pipeline that ingests and standardizes disparate data sources for early detection research.
1. Objective: To create a unified, analysis-ready dataset from multiple, non-standardized source systems (e.g., EHRs, lab systems, claims data) for the purpose of risk-based surveillance and early signal detection.
2. Experimental Workflow
The following diagram illustrates the logical flow and transformation stages of the data pipeline.
Diagram 1: Data pipeline workflow for surveillance
3. Materials and Reagents
Table 2: Research Reagent Solutions for Data Interoperability
| Item Name | Function/Description | Example Use Case |
|---|---|---|
| FHIR Server | A standards-based API for healthcare data exchange. | Acts as the core engine for receiving, storing, and providing access to data in a consistent FHIR format [52] [54]. |
| Terminology Server | Manages medical code systems (e.g., SNOMED CT, LOINC) and validates coded data. | Ensures semantic interoperability by mapping local codes to standard terminologies [52]. |
| ETL/ELT Tooling | Software for Extracting, Transforming, and Loading data. | Automates the data ingestion and transformation process from source systems into the unified repository. |
| Data Model Templates | Pre-defined templates for CDISC SDTM, OMOP CDM, etc. | Accelerates the structuring of data for specific research contexts, such as clinical trials or observational studies [55] [53]. |
4. Step-by-Step Procedure
- Source System Profiling: Catalog all potential data sources. For each source, document the data format, volume, update frequency, and the specific data elements relevant to surveillance (e.g., patient demographics, lab results, diagnostic codes).
- Standards Mapping: Define a target data model (e.g., FHIR, CDISC). Create a detailed mapping document that specifies how each field from each source system transforms into the target model. This is critical for addressing semantic inconsistency.
- Pipeline Implementation: a. Ingestion: Configure connectors to pull data from sources periodically or in real-time. b. Transformation: Implement the logic defined in the mapping document. This includes data type conversion, value normalization, and terminology mapping using the terminology server. c. Loading: Insert the transformed records into the unified repository (e.g., a database that supports the FHIR standard).
- Quality Validation: Establish automated checks for data quality, including completeness, conformity to the standard, and plausibility. This step is essential for ensuring the reliability of downstream surveillance analytics.
Protocol 2: Optimizing Spatial Surveillance Resource Deployment
This protocol adapts a model-based approach for determining the optimal placement of surveillance sites to maximize the probability of early pathogen detection, a common need in plant and human health.
1. Objective: To identify which arrangement of a fixed number of surveillance sites maximizes the probability of detecting an invading pathogen before it reaches a maximum acceptable prevalence [8] [9].
2. Experimental Workflow
The workflow combines spatial modeling with optimization to inform surveillance strategy.
Diagram 2: Workflow for optimizing surveillance site deployment
3. Materials and Reagents
Table 3: Research Reagent Solutions for Spatial Surveillance
| Item Name | Function/Description | Example Use Case |
|---|---|---|
| Spatially Explicit Model | A mathematical model simulating pathogen entry and spread through a landscape. | Used to generate multiple stochastic realizations of an outbreak [8] [9]. |
| Detection Sensitivity Parameters | The probability of correctly identifying an infected host/ sample. | A key input for the detection model, varying by diagnostic method (e.g., PCR, symptom inspection) [8] [56]. |
| Optimization Routine | A computational algorithm (e.g., Simulated Annealing). | Evaluates different arrangements of surveillance sites to find the one that maximizes the probability of early detection [8] [9]. |
| Geographic Information System (GIS) | Software for working with spatial data. | Used to manage and visualize the host landscape, risk maps, and optimal site locations. |
4. Step-by-Step Procedure
- Model Parameterization: a. Landscape: Define the geographic area of interest as a grid. Populate each cell with host density data (e.g., human population, citrus tree density) [9]. b. Introduction Risk: Define the spatial distribution of pathogen entry risk (e.g., higher at major travel hubs). c. Spread Dynamics: Parameterize the model with estimates for the reproduction number (R0) and dispersal kernel of the pathogen [56]. d. Detection: Define the performance characteristics of the detection method (sensitivity, sampling frequency, number of hosts sampled per site) [8].
- Outbreak Simulation: Run the spatial model repeatedly (e.g., 10,000 times) to generate a suite of potential outbreak scenarios, recording the time of infection for each grid cell in each simulation.
- Detection Assessment: For a given arrangement of surveillance sites, calculate the probability of detection as the proportion of simulations where the pathogen was detected at these sites before the prevalence threshold was crossed.
- Optimization: Use a stochastic optimization algorithm (e.g., simulated annealing) to search the space of possible site arrangements. The algorithm iteratively proposes new arrangements and evaluates them via the detection assessment step, moving towards an arrangement that maximizes the detection probability.
The Scientist's Toolkit
Table 4: Essential Standards and Technologies for Interoperable Surveillance
| Tool / Standard | Category | Primary Function in Research |
|---|---|---|
| FHIR (Fast Healthcare Interoperability Resources) | Data Exchange Standard | Provides a modern, API-based framework for exchanging healthcare data, enabling real-time data access for surveillance applications [52] [54]. |
| CDISC (e.g., SDTM, ADaM) | Clinical Data Standard | Defines structured formats for clinical trial data, ensuring consistency and regulatory compliance from protocol (via ICH M11) to submission [55] [53]. |
| ICH M11 (Clinical Trial Protocol Template) | Protocol Standardization | Establishes a structured, machine-readable format for clinical trial protocols, enhancing interoperability from the study's inception [55]. |
| ISO IDMP (Identification of Medicinal Products) | Product Data Standard | Suite of standards for uniquely identifying medicinal products, critical for pharmacovigilance and safety surveillance [53]. |
| SNOMED CT | Clinical Terminology | A comprehensive clinical terminology that provides the semantic standard for coding clinical concepts, enabling accurate data aggregation and analysis [52]. |
| Data Mesh/Fabric Architecture | Organizational & Tech Strategy | Conceptual frameworks for managing decentralized, domain-oriented data (Mesh) or providing a unified data layer (Fabric), helping overcome data silos [53]. |
Harmonizing Global Surveillance Methods for Enhanced Data Comparability
The harmonization of global surveillance methods is a critical foundation for effective public health action and scientific research. The increasing threat of antimicrobial resistance (AMR) and emerging infectious diseases necessitates coordinated, international efforts to strengthen data comparability across regions and institutions. A cornerstone of this effort is the Global Antimicrobial Resistance and Use Surveillance System (GLASS), established by the World Health Organization (WHO) in 2015. GLASS was created as a direct response to the Global Action Plan on AMR, with the objective to "strengthen knowledge through surveillance and research" and to fill critical knowledge gaps by informing strategies at all levels [57]. This system represents a paradigm shift from surveillance based solely on laboratory data to an integrated approach that incorporates epidemiological, clinical, and population-level data, thereby providing a more comprehensive understanding of disease dynamics and resistance patterns.
The fundamental challenge driving the need for harmonization is the inherent variability in data collection, analysis, and reporting methodologies across different jurisdictions and research groups. This variability was starkly demonstrated in a neuroimaging study comparing 21 different manual segmentation protocols for hippocampal subfields, which found substantial disagreement in anatomical labeling, particularly at the CA1/subiculum boundary and in the anterior portion of the hippocampal formation [58]. Such protocol heterogeneity creates significant barriers to comparing results across studies and pooling data for larger, more powerful analyses. The WHO's STEPwise approach to surveillance (STEPS) for noncommunicable diseases offers another successful model of harmonization, using a standardized but flexible framework that has been implemented in 122 countries across all six WHO regions [59]. This approach demonstrates that effective harmonization balances rigorous standardization with necessary adaptability to local contexts and resource constraints.
Optimized Risk-Based Surveillance for Early Detection: An Experimental Protocol
Theoretical Foundation and Principles
Risk-based surveillance represents a strategic approach for the early detection of emerging health threats by prioritizing resources toward geographical areas or populations judged most likely to contain the target pathogen. However, conventional risk-based strategies often rely on static "high-risk" classifications that fail to account for the dynamic epidemiological processes governing pathogen entry and spread. A groundbreaking approach developed by Mastin et al. (2020) addresses this limitation by combining spatially explicit models of pathogen entry and spread with statistical models of detection and stochastic optimization routines [8] [9]. This methodology answers the pivotal question: "Where exactly should surveillance resources be located to maximise the probability of detecting an invading pathogen before it reaches a certain prevalence threshold?"
A key insight from this research is that it is not always optimal to target only the highest-risk sites. The study revealed that spatial correlation in risk can make it suboptimal to focus solely on the highest-risk locations, demonstrating that sometimes "putting all your eggs in one basket" is an ineffective strategy [8] [9]. The optimal surveillance strategy depends on an interplay of factors including pathogen entry patterns, spread dynamics, and the technical characteristics of available detection methods. This approach was empirically validated using the economically devastating arboreal disease huanglongbing (HLB, also known as citrus greening) as a case study, showing significant performance gains and cost savings compared to conventional targeted surveillance methods.
Detailed Experimental Protocol
Model Parameterization and Setup
Objective: To establish a spatially explicit, stochastic model of pathogen spread through a real-world landscape.
- Landscape Grid Formation: Divide the geographic area of interest into a gridded landscape of 1 km × 1 km cells. Each cell should be populated with host density data informed by available agricultural, environmental, and demographic datasets [8].
- Pathogen Introduction Parameters: Define the frequency and spatial distribution of pathogen introduction events based on known risk factors such as trade routes, transportation networks, or historical introduction data.
- Transmission Dynamics: Parameterize secondary (between-cell) spread using an exponential dispersal kernel fitted to available epidemiological data. The model should account for increasing infectiousness and detectability over time post-infection [8].
- Threshold Establishment: Set a predefined "maximum acceptable prevalence" threshold that, when exceeded, terminates simulation runs. This threshold should reflect operational targets for early detection and should be informed by factors including pathogen epidemiology, potential impact, and available control measures.
Surveillance Optimization Procedure
Objective: To identify the optimal arrangement of surveillance sites that maximizes probability of early detection.
- Simulation Execution: Run the stochastic spatial model repeatedly (minimum 1,000 iterations) until the prevalence threshold is reached, capturing the inherent variability in spatiotemporal spread patterns.
- Detection Probability Modeling: For each potential arrangement of surveillance sites, calculate the probability of detection based on:
- Number of surveillance sites (Ω)
- Number of hosts sampled per site (n)
- Sampling frequency (Δt)
- Diagnostic sensitivity of the detection method
- Temporal growth in detectability following infection
- Optimization Routine: Apply a stochastic optimization algorithm (e.g., simulated annealing) to identify which arrangement of a specified number of sites yields the highest mean probability of detection across all simulation iterations [8].
- Strategy Validation: Compare the performance of the optimized surveillance strategy against conventional risk-based approaches in terms of detection probability, time to detection, and resource requirements.
Workflow Visualization
Figure 1: Workflow for optimizing risk-based surveillance strategies, integrating spatial modeling with stochastic optimization to maximize early detection probability.
Key Global Surveillance Systems: Architectures and Data Comparability
Comparative Analysis of Major Surveillance Frameworks
Table 1: Comparative analysis of major global surveillance systems and their harmonization approaches.
| System Name | Leading Organization | Primary Focus | Harmonization Method | Participating Countries | Key Harmonization Features |
|---|---|---|---|---|---|
| GLASS | WHO | Antimicrobial resistance | Standardized data collection, analysis, and interpretation protocols [57] | 109 countries and territories (as of May 2021) [57] | Modular technical structure; Integration of epidemiological and laboratory data; WHO-supported capacity building |
| STEPS | WHO | Noncommunicable disease risk factors | Stepwise framework with core, expanded, and optional modules [59] | 122 countries across all WHO regions [59] | Standardized instruments with flexibility for resource constraints; Electronic data collection (eSTEPS); Multistage cluster sampling |
| GLASS Regional Networks (CAESAR, EARS-Net, ReLAVRA) | WHO Regional Offices | Antimicrobial resistance | Regional adaptation of GLASS principles [57] | Varies by region | Regional coordination with global alignment; Shared databases and reporting standards |
| Influenza Surveillance (FluView) | CDC | Influenza viruses | Weekly reporting of standardized metrics [60] | Primarily U.S. with global coordination | Laboratory test standardization; Syndrome surveillance integration; Virus characterization protocols |
Quantitative Surveillance Metrics and Performance Indicators
Table 2: Representative surveillance data outputs demonstrating harmonized reporting formats across different systems.
| Surveillance System | Core Metrics Collected | Reporting Frequency | Data Aggregation Level | Representative Output (Source) |
|---|---|---|---|---|
| GLASS | AMR incidence, antimicrobial consumption, resistance patterns | Annual | National, regional, global | Global reports on AMR burden and trends [57] |
| CDC FluView | Percent positivity, virus characterization, geographic spread, severity indicators | Weekly | Regional, national | Wk 45, 2025: 2.0% positivity (867/42,928 specimens); 93.1% influenza A [60] |
| STEPS | Tobacco use, alcohol consumption, diet, physical activity, blood pressure, BMI, blood glucose | Variable (typically 3-5 years) | National with age and sex disaggregation | National NCD risk factor prevalence reports [59] |
| Optimized Risk Surveillance | Detection probability, time to detection, spatial distribution of positive findings | Continuous monitoring with regular evaluation | Implementation-specific | Case study: 30% performance gain in HLB detection vs conventional methods [8] |
The Researcher's Toolkit for Surveillance Harmonization
Essential Research Reagent Solutions
Table 3: Key reagents, tools, and platforms supporting harmonized surveillance activities across different domains.
| Tool/Reagent Name | Function/Purpose | Application Context | Implementation Considerations |
|---|---|---|---|
| WHONET Software | Microbiology laboratory data management and analysis with focus on AMR surveillance [57] | GLASS implementation; Hospital and public health laboratories | Free Windows application; Available in 28 languages; Used in 130+ countries |
| eSTEPS Platform | Electronic data collection for NCD risk factor surveys [59] | STEPS surveys; Population-based risk factor assessment | Supports handheld PCs and Android devices; Automated skip patterns and error checking |
| GLASS IT Platform | Web-based platform for global AMR and AMC data sharing [57] | National AMR surveillance reporting; Integrated analysis of AMC and AMR data | Common environment for data submission; Supports multiple technical modules |
| Spatial Optimization Algorithms | Computational identification of optimal surveillance site arrangements [8] | Early detection surveillance for emerging pathogens | Requires spatially explicit transmission models; Computational resource intensive |
| External Quality Assurance (EQA) Programs | Quality assessment of laboratory testing performance [57] | AMR testing standardization; Laboratory capacity building | Essential for cross-laboratory comparability; Coordinated by WHO Collaborating Centres |
Strategic Implementation Framework
Figure 2: Logical framework for implementing harmonized surveillance systems, showing the sequential relationship between core components that transform standardized protocols into public health action.
The harmonization of global surveillance methods represents an essential strategy for enhancing early detection capabilities and facilitating robust cross-jurisdictional comparisons. The frameworks and protocols outlined in this document provide actionable guidance for researchers and public health professionals implementing risk-based surveillance strategies. As surveillance technologies continue to evolve, future harmonization efforts must prioritize interoperability between systems, standardization of data exchange formats, and development of adaptable protocols that can accommodate emerging pathogens and changing epidemiological contexts. The integration of modeling and optimization approaches with traditional surveillance methods presents a promising avenue for enhancing the efficiency and effectiveness of global health protection efforts in an increasingly interconnected world.
The Critical Role of Capacity Building and Cross-Functional Collaboration
Application Note: Advancing Risk-Based Surveillance for Early Detection
Risk-based surveillance represents a paradigm shift in public health and drug development, moving from blanket monitoring to strategically targeted resource deployment. This approach maximizes the probability of early pathogen detection while optimizing limited financial and logistical resources [8]. Effective risk-based surveillance requires two foundational pillars: systematic capacity building to ensure sustained technical expertise and robust cross-functional collaboration to integrate diverse data streams and perspectives [61] [62]. Together, these elements enable researchers and drug development professionals to anticipate, detect, and respond to emerging health threats with greater speed and precision, ultimately strengthening global health security.
The critical importance of this approach is underscored by recent analyses of disease surveillance capabilities across multiple countries, which identified shared priority areas for action: capacity building through national training agendas; appropriate data tools and technology; clear data sharing standards; and genomic sequencing infrastructure [61]. Similarly, in conflict zones where infectious disease outbreaks are particularly devastating, technological innovations in surveillance are proving essential for overcoming compromised healthcare infrastructure and population displacement [62].
Quantitative Evidence Supporting Integrated Approaches
Table 1: Documented Benefits of Cross-Functional Collaboration in Technical Fields
| Performance Metric | Improvement | Context | Source |
|---|---|---|---|
| Time-to-Market | 25% faster delivery | Software development teams | [63] |
| Innovation Output | 20% more innovative solutions | Teams combining diverse perspectives | [63] |
| Product Quality | 30% reduction in critical defects | Early detection through collaboration | [63] |
| Customer Satisfaction | 35% higher satisfaction ratings | Products from integrated teams | [63] |
| Resource Utilization | 40% reduction in redundant work | Shared knowledge across functions | [63] |
Table 2: Shared Challenges in Disease Surveillance Capacity Building Across Five Countries
| Priority Area | Common Challenge | Recommended Action | Citation |
|---|---|---|---|
| Capacity Building & Training | Lack of sustainable training agenda | Develop national training agenda to guide donor-funded offers | [61] |
| Data Tools & Technology | Difficulty selecting appropriate software | Create decision frameworks for tool selection based on country needs | [61] |
| Data Sharing | Unclear standards for data exchange | Establish clear data sharing standards and norms from national to international levels | [61] |
| Genomic Sequencing | Absence of national strategies | Develop national genomic surveillance strategies and reporting guidelines | [61] |
Protocol: Implementing an Optimized Risk-Based Surveillance Framework
Capacity Building Protocol for Surveillance Systems
Objective
Establish sustainable technical capabilities for risk-based surveillance through standardized competency development, addressing critical gaps in training agendas, data tools, data sharing, and genomic sequencing identified across multiple national systems [61].
Materials and Reagents
Table 3: Essential Research Reagents and Solutions for Genomic Surveillance
| Item | Function/Application | Specification Notes |
|---|---|---|
| Nucleic Acid Extraction Kits | Pathogen RNA/DNA isolation | Ensure compatibility with diverse sample matrices (blood, tissue, environmental) |
| PCR Master Mix | Target pathogen amplification | Select based on required sensitivity and multiplexing capabilities |
| Next-Generation Sequencing Library Prep Kits | Genomic sequencing preparation | Consider throughput requirements and pathogen type (viral, bacterial) |
| Positive Control Panels | Assay validation and quality control | Should encompass genetic variants relevant to surveillance objectives |
| Point-of-Care Diagnostic Devices | Rapid field detection | Prioritize devices with connectivity for data integration |
Step-by-Step Methodology
Phase 1: Training Needs Assessment and Curriculum Development
- Conduct competency gap analysis: Survey current surveillance workforce across relevant disciplines (epidemiology, bioinformatics, laboratory science, data management) to identify specific technical skill deficiencies [61].
- Map to surveillance objectives: Align training priorities with the core functions of the risk-based surveillance system, emphasizing early detection capabilities.
- Develop modular curriculum: Create training modules addressing: (a) risk-based surveillance principles; (b) data management and analysis; (c) genomic sequencing technologies; (d) data sharing protocols and ethics [61] [62].
- Establish certification standards: Define proficiency benchmarks for key technical roles to ensure training effectiveness.
Phase 2: Technical Infrastructure Implementation
- Select and deploy data tools: Establish criteria for surveillance software selection, prioritizing interoperability, scalability, and alignment with country-specific needs [61].
- Implement genomic sequencing capacity: Develop national strategies for genomic surveillance, including equipment procurement, standardized operating procedures, and reporting guidelines [61].
- Create data sharing frameworks: Establish clear data sharing protocols that balance accessibility with security and privacy concerns, particularly important in conflict settings [62].
Phase 3: Sustainability Planning
- Develop training-of-trainers programs: Create master trainer cohorts to ensure ongoing knowledge transfer independent of external consultants.
- Integrate with academic institutions: Embed surveillance curricula in relevant university programs to create pipeline of future professionals.
- Secure dedicated funding: Identify sustainable financing mechanisms beyond donor funding to maintain capacity building activities [61].
Cross-Functional Collaboration Protocol for Surveillance Teams
Objective
Establish structured frameworks for effective cross-functional collaboration among surveillance stakeholders, breaking down departmental silos to enhance detection capabilities and response coordination.
Materials
- Collaboration platforms (Slack, Microsoft Teams, GitHub)
- Project management systems (JIRA, Asana, Monday)
- Documentation repositories (Confluence, Notion, GitBook)
- Design-development handoff tools (Figma, Zeplin)
- Video conferencing solutions with recording capability
Step-by-Step Methodology
Phase 1: Team Formation and Alignment
- Define clear purpose and strategic focus: Articulate the specific surveillance objectives the cross-functional team will address, ensuring alignment with broader public health goals [64].
- Select members based on collaborative competence: Identify participants from relevant functions (epidemiology, laboratory science, data analytics, clinical research, field operations) evaluating not only technical expertise but also demonstrated collaborative mindset, emotional intelligence, and commitment to shared success [64].
- Appoint facilitative leadership: Designate team leads based on facilitation skills rather than hierarchical authority, prioritizing abilities in maintaining alignment, managing competing priorities, creating psychological safety, and tracking dependencies [64].
- Define roles with explicit decision authorities: Utilize RACI (Responsible, Accountable, Consulted, Informed) matrices or similar frameworks to clarify decision-making roles and communication protocols [64].
Phase 2: Operational Integration
- Establish shared KPIs: Move beyond department-specific metrics to unified success measures focused on surveillance outcomes (e.g., time to detection, accuracy of risk forecasting, completeness of data integration) [63].
- Create unified workflows: Develop integrated processes that span traditional functional boundaries, such as combined data analysis and interpretation sessions with both field epidemiologists and bioinformaticians [63].
- Implement structured communication rhythms: Institute regular cross-functional stand-ups, sprint planning, and retrospective meetings specifically focused on surveillance activities and interdependencies [64].
- Leverage collaboration technology: Deploy integrated platforms that support cross-functional workflows, ensuring seamless information flow between field data collection, laboratory analysis, and data interpretation functions [63].
Phase 3: Culture and Relationship Building
- Define shared cultural beliefs: Establish practical, actionable behavioral norms (e.g., "I share updates proactively, even if things are still in progress") to guide cross-functional interactions [64].
- Create opportunities for informal interaction: Facilitate relationship-building across functions through both virtual and in-person forums to strengthen trust and communication.
- Celebrate collaborative successes: Recognize and reward behaviors that demonstrate effective cross-functional collaboration and contribute to improved surveillance outcomes.
Experimental Protocol: Optimizing Surveillance Site Selection
Objective
Implement a spatially explicit optimization approach for surveillance resource deployment that maximizes early detection probability for invading pathogens, moving beyond conventional risk-based targeting [8].
Materials
- Geospatial mapping software (QGIS, ArcGIS)
- Statistical computing environment (R, Python with appropriate spatial packages)
- Host population distribution data (commercial and residential densities)
- Pathogen dispersal parameter estimates
- Detection method sensitivity specifications
Step-by-Step Methodology
Landscape Parameterization:
- Develop a gridded landscape representation (e.g., 1km × 1km cells) incorporating host density data from both commercial and residential sources [8].
- Incorporate spatial heterogeneity in introduction risk based on known entry pathways (e.g., travel patterns, trade routes, vector distributions).
Pathogen Spread Modeling:
- Implement a stochastic, spatially explicit model of pathogen entry and spread through the host landscape [8].
- Parameterize secondary spread using exponential dispersal kernels fitted to empirical data where available.
- Continue simulations until a predefined maximum acceptable prevalence threshold is exceeded.
Detection Probability Calculation:
- For each potential surveillance site arrangement, calculate detection probability based on:
- Sampling intensity (number of hosts assessed per site)
- Sampling frequency (time between sampling events)
- Diagnostic sensitivity of detection methods
- Temporal progression of detectability post-infection
- For each potential surveillance site arrangement, calculate detection probability based on:
Optimization Routine:
- Apply stochastic optimization algorithms (e.g., simulated annealing) to identify surveillance site arrangements that maximize mean probability of detection across all model realizations [8].
- Validate optimized arrangements against conventional targeting approaches focused solely on highest-risk sites.
Performance Assessment:
- Compare detection probability and cost efficiency between optimized surveillance designs and conventional risk-based approaches.
- Evaluate robustness of optimized designs to uncertainties in pathogen introduction patterns and spread parameters.
Integration and Workflow Visualization
Diagram 1: Integrated surveillance system workflow showing the interconnection between capacity building, collaboration, and operational protocols.
Diagram 2: Collaborative surveillance governance structure showing multi-stakeholder engagement and data flow.
Measuring Impact: Validation Frameworks and Comparative Evaluations
Evaluating the performance of public health surveillance systems is fundamental to ensuring they effectively monitor health events and facilitate timely interventions. According to the Centers for Disease Control and Prevention (CDC) guidelines, the evaluation of surveillance systems should promote the best use of public health resources by ensuring that only important problems are under surveillance and that systems operate efficiently [65]. A well-performing surveillance system is particularly critical within risk-based surveillance strategies, where resources are deliberately allocated to areas with the highest probability of detecting health threats, thereby enhancing the likelihood of early outbreak detection and control [8] [66]. The core rationale underpinning these strategies is that issues presenting higher risks merit higher priority for surveillance resources as these investments yield higher benefit-cost ratios [66].
Surveillance systems vary widely in methodology, scope, and objectives. Therefore, their success depends on a proper balance of key performance attributes. Efforts to improve one attribute—such as the ability of a system to detect a health event (sensitivity)—may detract from others, such as simplicity or timeliness [65]. This application note provides a structured framework for quantifying the performance of surveillance systems through defined metrics, detailed protocols for evaluation, and visualization of key processes, all contextualized within the specific needs of early detection research.
Core Quantitative Metrics for Performance Evaluation
The performance of a surveillance system is multi-faceted and cannot be captured by a single metric. The CDC guidelines outline several key attributes that combine to affect a system's overall usefulness and cost [65]. The table below summarizes the core quantitative and qualitative metrics used for evaluation.
Table 1: Core Performance Attributes for Surveillance Systems
| Attribute | Definition | Quantitative/Qualitative Measures | Application in Risk-Based Strategies |
|---|---|---|---|
| Sensitivity | The ability of the system to detect all true cases or outbreaks of the health event [65] [21]. | Proportion of true cases detected by the system; ability to detect epidemics [65] [67]. | Optimized by targeting high-risk sub-populations where disease prevalence is expected to be higher [66] [21]. |
| Predictive Value Positive (PVP) | The proportion of reported cases that are true cases [65]. | Proportion of reported cases that are true cases; proportion of reported epidemics that are true epidemics [65] [67]. | High PVP ensures efficient resource use by minimizing false alarms during follow-up of reports [65]. |
| Timeliness | The speed between steps in a surveillance system [65]. | Time from disease onset to case reporting; to data analysis; and to intervention [65] [67]. | Critical for early detection, allowing control activities to be initiated before an outbreak exceeds a maximum acceptable prevalence [8] [21]. |
| Representativeness | The accuracy of the system in describing the occurrence of a health event over time and its distribution in the population by place and person [65]. | Ability to measure the natural history of the disease and store data on clinical outcomes [67]. | Ensures surveillance data from targeted, high-risk groups can be validly extrapolated to inform broader public health action [65] [66]. |
| Simplicity | Refers to both the system's structure and its ease of operation [65]. | Number of reporting sources; staff training requirements; type and extent of data analysis [65]. | Complex risk models must be balanced against the need for operational simplicity to ensure sustainability [65]. |
| Flexibility | The ability of the system to adapt to changing information needs or operating conditions with minimal additional cost [65] [67]. | Ability to handle new health-related events and integrate with other systems [67]. | Allows the system to incorporate new risk factors or adapt to emerging threats [65]. |
| Acceptability | The willingness of individuals and organizations to participate in the surveillance system [65]. | Completion rates of case report forms; laboratory completion rates; participation rates of hospitals [67]. | Fundamental for data quality, especially in systems relying on voluntary reporting from healthcare providers [65]. |
| Usefulness | The degree to which the system contributes to the prevention and control of adverse health events [65]. | Documented actions taken as a result of surveillance data; stimulation of research; assessment of control measures [65] [67]. | The ultimate goal of a risk-based system, justifying its cost by demonstrating impact on health outcomes [65] [66]. |
Advanced and Composite Metrics
Beyond the fundamental attributes, more advanced metrics are essential for a nuanced assessment, particularly for chronic diseases or early detection.
- Case-Finding Indices: For chronic diseases with long subclinical periods, the commonly used ratio of detected cases to total cases (p₂/(p₁+p₂)) can be misleading. A more valid index is the ratio of undetected cases to persons without a diagnosis (p₁/(p₀+p₁)), which reflects the prevalence within the "search space" for new cases [68]. Furthermore, incidence-based measures derived from multi-state models are preferable to prevalence-based indicators for assessing the performance of case-finding over time [68].
- Probability of Detection: For early detection of invasive pathogens, performance can be quantified as the probability that a surveillance system detects an invading pathogen before it reaches a predefined maximum acceptable prevalence. This probability is a function of population coverage, temporal coverage, and the diagnostic sensitivity of the detection method [8] [21].
- System Stability: This refers to the reliability (ability to collect, manage, and provide data without failure) and availability of the public health surveillance system. It can be assessed by measuring system downtimes and the resources required for technical repairs [67].
Application Note: Protocol for Evaluating and Optimizing an Early Detection Surveillance System
This protocol provides a step-by-step methodology for evaluating the performance of a surveillance system designed for the early detection of a known high-consequence pathogen, such as Candidatus Liberibacter asiaticus (causing citrus greening) [8] or a veterinary pathogen like Foot-and-Mouth Disease virus [21]. The process is cyclic, emphasizing continuous system improvement.
Phase 1: Foundational System Evaluation
This phase involves a comprehensive assessment of the existing surveillance system against established guidelines [65].
Table 2: Key Materials for Surveillance System Evaluation
| Research Reagent / Resource | Function / Application in Evaluation |
|---|---|
| Standardized Evaluation Questionnaire | A validated instrument based on CDC guidelines to systematically rate system attributes (e.g., simplicity, timeliness) on a Likert scale. Ensures consistent and comparable assessment [67]. |
| System Flowchart | A visual representation of information flow from case identification to report dissemination. Critical for assessing simplicity and identifying bottlenecks [65]. |
| Historical Surveillance Data | Archived case reports, laboratory results, and outbreak alerts. Used for calculating sensitivity, PVP, timeliness, and data quality metrics [65] [68]. |
| Stochastic Simulation Model | A spatially explicit model of pathogen entry and spread. Used to predict outbreak trajectories and test the performance of different surveillance strategies in silico [8]. |
| Costing Framework | A structured method to capture direct (staff, lab tests) and indirect (reporting burden) costs of operating the surveillance system. Essential for cost-effectiveness analysis [65] [66]. |
Procedure:
- Define Public Health Importance and System Objectives: Clearly articulate the health event under surveillance and the specific objectives of the system (e.g., detect outbreaks, monitor trends, identify contacts for prophylaxis) [65].
- Describe the System: Create a detailed description of all system components.
- Population under surveillance: Define the geographic and demographic scope.
- Case definition: State the standard criteria for confirming a case.
- Data flow: Construct a flow chart (as in Figure 1) depicting each step from case identification by a healthcare provider or laboratory, through information transfer and storage, to data analysis and dissemination of reports [65].
- Stakeholders: Identify all entities that provide, analyze, or use the surveillance data.
- Assess Usefulness: Document specific instances where surveillance data has led to concrete public health actions, such as triggering outbreak investigations, informing policy decisions, or assessing the impact of control measures. This demonstrates the system's real-world value [65].
- Quantify Performance Attributes: Using historical data and stakeholder input, calculate the metrics defined in Table 1.
- Sensitivity: If possible, compare cases detected by the system with an external "gold standard" estimate of total cases (e.g., from dedicated prevalence studies) [68].
- Timeliness: Measure the average number of days from symptom onset to case report receipt, and from report receipt to initiation of a public health response [65] [67].
- Data Quality: Assess the completeness and validity (e.g., accuracy, standardization) of data entered into the system [67].
- Analyze Resources: Compile all direct financial costs and personnel time required to operate the system. This provides the denominator for efficiency calculations [65].
- Formulate Conclusions and Recommendations: Conclude whether the system is meeting its objectives. Recommend whether to continue, modify, or terminate the system based on its usefulness, performance, and cost [65].
Phase 2: Risk-Based Optimization for Early Detection
This protocol details an advanced method for optimizing the spatial deployment of surveillance resources to maximize the probability of early detection, as demonstrated for huanglongbing (HLB) in citrus [8] [9].
Procedure:
- Define the Optimization Goal: Set a clear objective, such as: "Maximize the probability of detecting at least one infected host before the overall population prevalence exceeds a specified threshold (e.g., 0.1%)."
- Develop a Spatially Explicit Simulation Model:
- Landscape Parametrization: Create a gridded landscape map incorporating host density (e.g., commercial and residential citrus trees) and potential risk factors for pathogen entry (e.g., proximity to trade routes, airports) [8].
- Model Pathogen Introduction and Spread: Model primary introduction as a stochastic process, with higher introduction probabilities in high-risk cells. Model secondary spread using a dispersal kernel that defines how the pathogen moves between cells over time [8].
- Incorporate Detectability: For each grid cell, model the increase in detectability over time post-infection, which is a function of pathogen population growth and the diagnostic sensitivity of the detection method [8].
- Run Multiple Stochastic Simulations: Execute the model hundreds or thousands of times to generate a wide range of possible invasion scenarios, capturing the inherent uncertainty in pathogen introduction and spread. Each run continues until the maximum acceptable prevalence is exceeded [8].
- Apply an Optimization Algorithm:
- Use a computational optimization routine (e.g., simulated annealing) to test different arrangements of a fixed number of surveillance sites.
- The algorithm evaluates each arrangement by calculating the mean probability of detection across all simulation runs, given constraints like sampling frequency (Δt) and number of hosts sampled per site (n) [8].
- The output is the specific arrangement of surveillance sites (Ω) that maximizes the probability of early detection (p(Ω, n, Δt)).
- Validate and Implement the Optimal Strategy: Compare the performance of the optimized strategy against conventional risk-based targeting (e.g., sampling only the very highest-risk sites). Implement the optimized surveillance plan in the field.
Discussion and Interpretation of Results
The evaluation and optimization protocols provide a data-driven pathway to enhance surveillance performance. A key insight from recent research is that the optimal surveillance strategy is not always intuitive. For example, concentrating all resources on the single highest-risk site can be suboptimal if pathogen introductions are possible at multiple, spatially correlated locations. In such cases, "spreading the net" to cover several high-to-medium-risk sites can yield a higher overall probability of detection, effectively avoiding the pitfall of "putting all your eggs in one basket" [8]. The optimal strategy is a complex interplay between the patterns of pathogen entry and spread, the number of available surveillance sites, the frequency of sampling, and the diagnostic sensitivity of the detection method [8] [21].
Interpreting the results of an evaluation requires a holistic view where all attributes are balanced against the system's objectives and operational context. For instance, a system might have moderate sensitivity but high timeliness and acceptability, making it extremely useful for early detection. Conversely, a highly sensitive system that is complex, costly, and slow may fail to achieve its core purpose. The ultimate measure of success is the demonstrated usefulness of the system—its documented contribution to preventing and controlling adverse health events [65]. By adopting a rigorous, quantitative approach to performance measurement and leveraging modern computational methods for optimization, surveillance systems can be transformed into more efficient, effective, and responsive tools for protecting population health.
Comparative Analysis of International Surveillance Systems and Models
Surveillance systems are critical components of public health infrastructure, providing essential data for monitoring disease trends, detecting outbreaks, and guiding intervention strategies. The evolution of these systems has been significantly influenced by emerging technologies, particularly artificial intelligence (AI) and machine learning (ML), which have enhanced their predictive capabilities and operational efficiency. In the context of risk-based surveillance strategies for early detection, understanding the comparative strengths and limitations of various international surveillance models becomes paramount for researchers, scientists, and drug development professionals. This analysis examines diverse surveillance frameworks across multiple domains, focusing on their structural attributes, methodological approaches, and applicability to early detection research. The integration of AI technologies has transformed traditional surveillance paradigms, enabling more sophisticated analysis of complex datasets and improving the timeliness and accuracy of public health decision-making. Furthermore, the development of standardized evaluation criteria has facilitated more meaningful comparisons between systems, allowing researchers to select optimal surveillance strategies based on specific contextual requirements and operational constraints.
Comparative Analysis of Surveillance System Attributes
Evaluation frameworks provide critical guidance for assessing the performance and utility of surveillance systems. Established guidelines outline key attributes including simplicity, flexibility, acceptability, sensitivity, predictive value positive, representativeness, and timeliness [65]. These attributes combine to affect the overall usefulness and cost-effectiveness of surveillance systems, though their relative importance varies depending on system objectives and operational contexts.
Table 1: Core Attributes for Surveillance System Evaluation
| Attribute | Definition | Importance for Early Detection | Measurement Approaches |
|---|---|---|---|
| Timeliness | Speed between data collection and public health action | Critical for rapid response to emerging threats | Time from case detection to reporting and intervention |
| Sensitivity | Proportion of true cases detected by the system | High sensitivity enables early outbreak recognition | Comparison with validated case ascertainment methods |
| Specificity | Proportion of true non-cases correctly identified | Reduces resource waste on false alarms | Proportion of false positives among reported cases |
| Representativeness | Accuracy in reflecting population incidence | Ensures findings are generalizable to target population | Demographic comparison between surveilled and actual population |
| Coverage | Proportion of target population included | Affects accuracy of incidence estimates | Percentage of target population under surveillance |
| Robustness | System reliability under varying conditions | Ensures consistent performance during crises | System performance metrics during stress periods |
| Completeness | Proportion of data fields populated | Enhances analytical capabilities for risk stratification | Percentage of records with all required data elements |
| Historical Data | Availability of longitudinal data | Enables trend analysis and model training | Years of consistent data collection available |
Recent research has adapted these traditional evaluation frameworks to assess the suitability of surveillance systems for AI and ML applications. A 2025 study on influenza surveillance systems identified eight key attributes particularly relevant for predictive modeling: timeliness, sensitivity, specificity, representativeness, coverage, robustness, completeness, and historical data [69]. The study employed a weighted scoring system to evaluate systems for both training utility (emphasizing historical data, sensitivity, specificity, and completeness) and short-term forecasting utility (prioritizing timeliness, robustness, sensitivity, and specificity). This methodological approach demonstrates how evaluation criteria must be tailored to specific use cases, particularly when surveillance data is intended to feed predictive models for early detection.
The integration of AI technologies has introduced new dimensions for surveillance system evaluation. AI-driven systems must balance algorithmic performance with practical implementation considerations, including computational requirements, interoperability with existing infrastructure, and adaptability to evolving threats. Moreover, the emergence of explainable AI has become increasingly important for regulatory acceptance and practical utility in healthcare settings, particularly for drug development applications where understanding the rationale behind alerts is essential for clinical decision-making.
International Surveillance Models and Methodologies
Surveillance systems vary significantly in their design, implementation, and target applications across international contexts. These variations reflect differences in public health priorities, resource availability, and technological infrastructure. Below we examine several prominent models and their methodological approaches.
Disease-Specific Surveillance Frameworks
Influenza surveillance systems provide a well-established model for respiratory disease monitoring. A 2025 evaluation of New Zealand's influenza surveillance infrastructure identified ten distinct systems operating across community, hospital, and mortality levels [69]. The Southern Hemisphere Influenza and Vaccine Effectiveness Research and Surveillance (SHIVERS) community cohort and Severe Acute Respiratory Infection (SARI) hospital surveillance achieved the highest scores for both training and short-term forecasting capabilities. The study employed a two-phase methodology: first, comprehensive description of systems through government reports, official websites, and literature; second, evaluation against eight key attributes using a five-level ranking system with weighted scores to determine alignment with AI/ML requirements.
Table 2: Comparison of International Surveillance System Types
| System Type | Primary Data Sources | Best Applications | Key Strengths | Major Limitations |
|---|---|---|---|---|
| Influenza Surveillance Networks [69] | Laboratory tests, GP consultations, hospital admissions | Seasonal trend monitoring, vaccine effectiveness | Established infrastructure, international standardization | Limited to specific pathogens, seasonal focus |
| Wastewater Surveillance [70] | Municipal wastewater samples | Community-level pathogen tracking, early outbreak detection | Population-wide coverage, non-invasive, cost-effective | Complex standardization needs, limited individual-level data |
| Postmarketing Drug Surveillance [71] | Spontaneous reports, electronic health records, claims databases | Drug safety monitoring, adverse event detection | Regulatory mandate, large sample sizes, real-world evidence | Underreporting, signal validation challenges |
| Cancer Early Detection [47] | Medical imaging, biomarker tests, clinical parameters | High-risk population monitoring, treatment response | Specialized detection methods, risk stratification capabilities | High cost, requires specialized equipment and expertise |
| Plant Disease Surveillance [8] | Field surveys, sensor networks, satellite imagery | Agricultural protection, ecosystem monitoring | Geospatial components, economic impact focus | Limited integration with human health systems |
Wastewater Surveillance Standardization
Wastewater surveillance has emerged as a critical tool for community-level monitoring, particularly during the COVID-19 pandemic. However, methodological variations present challenges for data comparability. A novel approach termed the "Data Standardization Test" enables quantitative comparison of wastewater surveillance data across different analytical methods without requiring method standardization [70]. This protocol utilizes non-spiked, field-collected wastewater samples as reference materials to measure relative quantification biases across laboratories. The methodology involves:
- Reference Sample Distribution: Identical wastewater samples containing naturally occurring target pathogens are distributed to participating laboratories.
- Parallel Analysis: Each laboratory processes samples according to their standard operating procedures.
- Bias Factor Calculation: Method-specific bias correction factors are derived by comparing results across laboratories.
- Data Standardization: Routine surveillance data are adjusted using these factors to enable cross-method comparison.
This approach has demonstrated effectiveness in standardizing SARS-CoV-2 and pepper mild mottle virus (PMMoV) RNA quantification across seven different lab-assay combinations, significantly improving data comparability without constraining methodological choices [70].
AI-Enhanced Early Detection Systems
Artificial intelligence has dramatically transformed surveillance capabilities, particularly for early detection applications. In hepatocellular carcinoma (HCC) surveillance, deep learning models have shown remarkable potential for improving risk stratification and early detection. The STARHE system incorporates two complementary AI models: STARHE-RISK for HCC risk stratification using ultrasound cine clips of non-tumoral liver parenchyma, and STARHE-DETECT for early-stage HCC detection using tumor ultrasound cine clips [47].
The experimental protocol for developing these models involved:
- Study Population: 403 adult patients with compensated advanced chronic liver disease without prior HCC history.
- Data Collection: Prospective multicenter collection of ultrasound cine clips.
- Model Architecture: Deep learning models trained on parenchymal and tumor imaging features.
- Validation: Stratified training/validation and testing sets with independent testing on balanced patient groups.
The resulting models achieved significant performance improvements, with STARHE-RISK demonstrating an accuracy of 0.72 (95% CI 0.57-0.84) and an odds ratio of 6.6 (95% CI 1.9-22.7) for predicting HCC risk [47]. When combined with the FASTRAK clinical score, specificity improved to 0.86 (95% CI 0.65-0.97), highlighting the value of integrating multiple data modalities in surveillance systems.
Experimental Protocols for Surveillance System Development
Risk-Based Surveillance Optimization
Optimizing risk-based surveillance requires sophisticated methodological approaches that account for spatial heterogeneity and resource constraints. A 2020 study developed a novel framework for optimizing risk-based surveillance for early detection of plant pathogens, with methodology applicable to infectious disease surveillance [8]. The protocol integrates a spatially explicit model of pathogen entry and spread with a statistical model of detection, using stochastic optimization to identify surveillance arrangements that maximize detection probability.
The experimental workflow involves:
Figure 1: Risk-Based Surveillance Optimization Workflow
This methodology revealed that conventional approaches of targeting only the highest-risk sites are often suboptimal, with better performance achieved by accounting for spatial correlation in risk and avoiding excessive concentration of resources [8]. The optimization framework significantly outperformed conventional risk-based targeting, demonstrating the value of computational approaches for surveillance planning.
Quality and Safety Surveillance Development
The development of comprehensive quality and safety surveillance systems in healthcare requires systematic approaches to address complex implementation challenges. A protocol for a rapid realist review aims to develop a program theory for quality and safety surveillance system development [72]. The methodology includes:
- Initial Program Theory Development: Based on literature review, stakeholder consultations, and systems theory.
- Iterative Searching: Three-phase searches across multiple databases (PubMed, PsycInfo, Central, CINAHL) and grey literature.
- Data Extraction and Synthesis: Identification of context-mechanism-outcome (CMO) configurations.
- Theory Refinement: Developing and refining explanatory theories about what works for whom under what circumstances.
This approach acknowledges that successful surveillance system implementation depends not only on technical specifications but also on contextual factors including organizational culture, resources, and stakeholder engagement [72].
Signaling Pathways and Conceptual Frameworks
Surveillance systems operate through conceptual frameworks that integrate data sources, analytical processes, and decision-making pathways. The signaling pathway for AI-enhanced surveillance systems illustrates the flow from data collection to public health action.
Figure 2: AI-Enhanced Surveillance Signaling Pathway
This framework highlights the critical role of feedback loops in continuously improving surveillance system performance based on outcome assessments. The integration of multiple data sources enables more robust risk stratification, while AI analytics enhance the sensitivity and timeliness of alert generation [69] [47].
Research Reagent Solutions for Surveillance Applications
The implementation of effective surveillance systems requires specific methodological tools and analytical resources. The following table details essential research reagents and their applications in surveillance research.
Table 3: Essential Research Reagents for Surveillance Studies
| Reagent/Resource | Primary Function | Application Context | Technical Specifications |
|---|---|---|---|
| Reference Wastewater Samples [70] | Standardization across analytical methods | Wastewater surveillance | Field-collected, non-spiked samples with native pathogen content |
| Ultrasound Cine Clips [47] | Training AI detection models | Medical imaging surveillance | Standardized acquisition protocols, annotated lesion boundaries |
| Spatial Risk Maps [8] | Targeting surveillance resources | Geographical surveillance | High-resolution host distribution data, incorporation of dispersal kernels |
| AI Model Architectures [47] | Pattern recognition in complex data | AI-enhanced surveillance | Convolutional neural networks for imaging, transformer models for temporal data |
| Standardized Evaluation Metrics [69] [65] | System performance assessment | Surveillance quality control | Timeliness, sensitivity, specificity, PVP, representativeness scores |
| Data Integration Platforms [72] | Harmonizing multiple data sources | Multi-stream surveillance | Interoperability standards, API frameworks, common data models |
These research reagents enable the development, standardization, and optimization of surveillance systems across diverse applications. Reference materials like standardized wastewater samples facilitate quantitative comparison across laboratories and methods [70], while annotated imaging datasets support the training and validation of AI models for medical surveillance [47]. The availability of these essential resources directly impacts the quality, reliability, and comparability of surveillance data across different systems and jurisdictions.
This comparative analysis demonstrates significant advances in surveillance methodologies across international contexts and application domains. The integration of AI technologies has substantially enhanced early detection capabilities, particularly through improved risk stratification and pattern recognition in complex datasets. Furthermore, standardized evaluation frameworks enable more systematic comparison of system performance and identification of optimal approaches for specific surveillance objectives. The development of novel standardization methods, such as the Data Standardization Test for wastewater surveillance, addresses critical challenges in data comparability without constraining methodological choices. Optimization approaches that account for spatial heterogeneity and resource constraints demonstrate improved performance compared to conventional risk-based targeting strategies. For researchers and drug development professionals, these advances offer powerful tools for designing surveillance strategies that maximize early detection capabilities while efficiently utilizing available resources. Future directions will likely focus on enhancing interoperability between systems, developing more sophisticated AI analytics, and addressing ethical considerations in data-intensive surveillance approaches.
Risk-based surveillance represents a paradigm shift in public health and biosecurity, moving from blanket monitoring to targeted, intelligent resource allocation. This strategy involves identifying populations, geographical areas, or pathways judged most likely to contain pests or pathogens and preferentially directing inspection and sampling resources toward these high-priority targets [8]. The fundamental goal is to maximize the probability of early detection of invading epidemics before they exceed a manageable prevalence threshold, thereby enabling more effective and timely control interventions [8].
This approach is particularly crucial for emerging infectious diseases (EIDs) of plants, animals, and humans, which continue to devastate ecosystems and livelihoods worldwide [8]. The connectedness of modern populations through international travel and trade creates conditions favoring rapid global dispersal of new diseases, making early detection systems not merely beneficial but essential components of public health infrastructure [50]. By explicitly accounting for epidemiological processes and spatial dynamics, risk-based surveillance provides a framework for achieving early detection within the constraints of limited financial and logistical resources.
Theoretical Framework and Risk Assessment Methods
Effective risk-based surveillance relies on a systematic approach to risk identification, analysis, and evaluation. The theoretical foundation combines spatial epidemiology with statistical decision theory to optimize surveillance resource deployment.
Qualitative and Quantitative Risk Assessment
Risk assessment methodologies generally fall into two complementary categories: qualitative and quantitative approaches. Each offers distinct advantages and is suited to different contexts within pathogen surveillance.
Table 1: Comparison of Qualitative and Quantitative Risk Assessment Methods
| Feature | Qualitative Risk Assessment | Quantitative Risk Assessment |
|---|---|---|
| Basis | Expert judgment, experience, subjective evaluation [73] [74] | Numerical data, statistical analysis, objective measurements [73] [74] |
| Output | Relative rankings (e.g., high/medium/low), colors, priority scales [73] [75] | Numerical probabilities, financial impacts, measurable values [73] [75] |
| Advantages | Quick to implement, requires less data, useful for novel risks [74] [75] | Objective, actionable results, enables cost-benefit analysis [73] [74] |
| Limitations | Subjective, difficult to prioritize between similar ratings [73] | Data-intensive, time-consuming, may require specialized tools [73] [74] |
| Common Tools | Risk matrices, DREAD model, probability/impact grids [73] [75] | Decision trees, Monte Carlo analysis, Annualized Loss Expectancy (ALE) [75] |
Qualitative assessments are particularly valuable when risks are difficult to quantify, when dealing with emerging threats lacking historical data, or when facing complex, multifaceted risks that resist simple numerical expression [74]. The DREAD model exemplifies a structured qualitative approach, evaluating risks based on Damage potential, Reproducibility, Exploitability, Affected users, and Discoverability [73].
Quantitative analysis becomes feasible when sufficient data exists to assign numerical values to risk components. Key calculations include:
- Single Loss Expectancy (SLE): Asset Value × Exposure Factor [75]
- Annualized Rate of Occurrence (ARO): Expected frequency of occurrence per year [75]
- Annualized Loss Expectancy (ALE): SLE × ARO [75]
This quantitative framework enables direct comparison of risk mitigation options through cost-benefit analysis, helping decision-makers determine appropriate investments in surveillance and control measures [75].
Integration into Risk Management Lifecycle
Effective risk management follows a systematic lifecycle comprising seven key processes:
- Determine risk context, scope, and strategy
- Identify risks and prepare risk registers
- Perform qualitative analysis and select risks for detailed assessment
- Conduct quantitative analysis on selected risks
- Plan response measures and controls
- Implement chosen risk responses
- Monitor risk improvements and residual risk [75]
This structured approach ensures comprehensive coverage of the risk landscape and facilitates evidence-based decision-making for surveillance resource allocation.
Quantitative Data in Pathogen Surveillance
The application of quantitative methods to pathogen surveillance enables precise evaluation of intervention strategies and resource allocation decisions. The following table summarizes key quantitative metrics and their implications for surveillance design.
Table 2: Quantitative Metrics for Pathogen Surveillance Optimization
| Metric | Application Context | Values/Examples | Implications |
|---|---|---|---|
| Target Contrast Ratios | Visual inspection and diagnostic readability | 7:1 for normal text; 4.5:1 for large text (≥18.66px or 14pt bold) [76] | Ensures detection methods and interfaces are accessible under various conditions |
| Source Document Verification (SDV) Yield | Clinical trial data quality assessment | Only 1.1% of data corrected due to SDV findings; 3.7% overall correction rate [77] | Supports targeted rather than 100% verification, significantly improving efficiency |
| Spatial Risk Correlation | Surveillance site selection for early detection | Not always optimal to target only highest-risk sites [8] | Suggests "don't put all eggs in one basket" approach for detection probability |
| Pathogen Introduction Rate | Huanglongbing (HLB) citrus disease model | Varied introduction probabilities across locations [8] | Requires customizing surveillance intensity based on entry risk patterns |
| Detection Method Sensitivity | Surveillance system performance | Varies by diagnostic technique; influences optimal site arrangement [8] | Higher sensitivity may allow different spatial deployment strategies |
These quantitative insights demonstrate that conventional approaches to surveillance often yield suboptimal resource utilization. For example, the minimal impact of extensive SDV on final data quality challenges long-standing clinical trial monitoring practices, suggesting that redirected resources could enhance overall study integrity more effectively through alternative quality control measures [77].
Similarly, the finding that spatial correlation in risk can make it suboptimal to focus solely on the highest-risk sites has profound implications for surveillance network design. This counterintuitive result emerges from complex interactions between pathogen entry patterns, spread dynamics, and detection method characteristics [8].
Experimental Protocols and Methodologies
Protocol: Spat Explicit Pathogen Spread Simulation for Surveillance Optimization
Purpose: To identify optimal surveillance site arrangements that maximize probability of early pathogen detection before prevalence exceeds acceptable thresholds.
Materials:
- Geographic Information System (GIS) software with spatial analysis capabilities
- Host distribution data (e.g., commercial and residential citrus density maps)
- Pathogen introduction risk data (e.g., human movement patterns from infected areas)
- Computational resources for stochastic modeling
Procedure:
- Landscape Grid Establishment:
- Divide the region of interest into 1km × 1km grid cells
- Populate each cell with host density information from agricultural and census data [8]
Pathogen Introduction Parameterization:
- Model external introduction events as stochastic processes in continuous time
- Weight introduction probabilities by risk factors (e.g., proximity to transportation hubs, trade routes)
Secondary Spread Modeling:
- Implement between-cell spread using an exponential dispersal kernel
- Parameterize dispersal kernel using empirical pathogen-specific data
- Model increasing infectiousness and detectability over time post-infection
Surveillance Simulation:
- Define maximum acceptable prevalence threshold
- Run multiple stochastic simulations until prevalence threshold is exceeded
- Record detection status for various surveillance arrangements
Optimization Analysis:
- Use simulated annealing algorithm to identify surveillance arrangements maximizing detection probability
- Evaluate performance across different sampling intensities (n), frequencies (Δt), and detection sensitivities [8]
Validation:
- Compare optimized surveillance strategy performance against conventional risk-based targeting
- Calculate performance gains and cost savings relative to traditional methods
Protocol: Risk-Based Monitoring for Clinical Trials
Purpose: To implement monitoring strategies commensurate with the identified risk level of clinical research, focusing resources on critical study aspects.
Materials:
- Risk assessment tool (e.g., ADAMON Risk Scale, OPTIMON Risk Scale) [77]
- Study protocol and investigational plan
- Data collection and management system
Procedure:
- Risk Identification and Categorization:
- Assess risks to participant safety and rights
- Evaluate risks to study result validity
- Consider organizational, governance, and operational risks [77]
Risk Level Determination:
Monitoring Strategy Selection:
Targeted Monitoring Implementation:
- Focus on key elements with highest impact on participant safety and data validity
- Replace 100% source document verification with risk-based approaches
- Implement centralized monitoring where appropriate
Reporting and Communication:
- Report serious adverse events to relevant authorities within specified timeframes
- Conduct regular team meetings to review adverse events and protocol issues
- Update Data and Safety Monitoring Plan as benefit-risk analysis evolves [78]
Workflow Visualization
The following diagram illustrates the integrated workflow for developing and implementing risk-based surveillance strategies:
Risk-Based Surveillance Development Workflow
Research Reagent Solutions Toolkit
The implementation of effective risk-based surveillance strategies requires both conceptual frameworks and practical tools. The following table details essential resources for developing and deploying risk-based pathogen surveillance.
Table 3: Research Reagent Solutions for Risk-Based Surveillance
| Tool/Resource | Function | Application Context |
|---|---|---|
| Spatially Explicit Stochastic Model | Simulates pathogen entry and spread through landscape; predicts detection probabilities [8] | Optimizing surveillance site arrangements for early detection |
| ADAMON Risk Scale | 3-level scale assessing patient safety risks and result validity risks [77] | Clinical trial risk assessment and monitoring intensity adaptation |
| OPTIMON Risk Scale | 4-level scale (A-D) based on intervention and investigation characteristics [77] | Adaptation of onsite monitoring intensity in clinical research |
| ECRIN Guidance Document | List of 19 study characteristics across 5 topics for risk identification [77] | Comprehensive risk assessment during clinical trial planning |
| Risk-Based Monitoring Score Calculator | 3-level scale based on intervention characteristics [77] | Determining monitoring intensity for non-commercial trials |
| Simulated Annealing Algorithm | Computational optimization to maximize detection probability [8] | Identifying optimal surveillance resource deployment |
| Logistics/Impact/Resources Score | Quantitative score (0-40) for logistics, impact and resource aspects [77] | Post-risk assessment monitoring intensity determination |
| DREAD Model | Qualitative assessment of Damage, Reproducibility, Exploitability, Affected users, Discoverability [73] | Structured evaluation of cybersecurity and other operational risks |
These tools enable researchers and public health professionals to implement the theoretical principles of risk-based surveillance in practical, actionable strategies. The combination of spatial modeling, risk assessment frameworks, and optimization algorithms provides a comprehensive toolkit for developing surveillance systems that maximize detection probability while efficiently utilizing available resources.
Risk-based strategies for pathogen control represent a significant advancement over traditional uniform surveillance approaches. By explicitly incorporating spatial dynamics, pathogen spread parameters, and resource constraints, these methods achieve higher detection probabilities and greater cost efficiency. The case study of huanglongbing (HLB) in Florida demonstrates how optimized surveillance strategies can significantly outperform conventional risk-based targeting, potentially leading to earlier detection and more effective control of invading pathogens [8].
The successful implementation of risk-based surveillance requires integration of qualitative and quantitative assessment methods, appropriate tool selection from the available reagent solutions, and continuous monitoring and adaptation of strategies based on performance feedback. As emerging infectious diseases continue to threaten global health and food security, these sophisticated, evidence-based approaches to surveillance will play an increasingly critical role in early detection and effective response.
Developing Standardized Frameworks for Cancer and Infectious Disease Surveillance
The escalating global burden of chronic and infectious diseases necessitates a paradigm shift from passive monitoring to proactive, intelligence-driven surveillance. Risk-based surveillance represents this advanced approach, strategically allocating finite resources to populations and geographical areas with the highest probability of disease occurrence or introduction. This methodology significantly enhances the efficiency and effectiveness of early detection systems, a cornerstone for effective public health intervention [8] [25]. For cancer, which accounts for approximately 10 million deaths annually, robust surveillance is indispensable for tracking epidemiological trends and guiding control strategies [79] [80]. Similarly, for infectious diseases, early detection of emerging pathogens is critical to prevent devastating outbreaks and ecosystem damage, as witnessed in the collapse of the American chestnut or the citrus industry in Florida due to huanglongbing (HLB) [8] [9].
The development of standardized frameworks ensures that data collected across different regions and systems are comparable, interoperable, and actionable. Such frameworks address critical gaps in traditional systems, which often lack on-demand analytics, spatial visualization, and predictive modeling capabilities [79]. By integrating advanced methodologies from both chronic and infectious disease domains, this protocol provides a unified approach for researchers and public health professionals to design, implement, and evaluate sophisticated risk-based surveillance systems capable of meeting modern public health challenges.
Experimental Protocols for Framework Development and Evaluation
Protocol 1: Systematic Development of a Cancer Surveillance Framework
This protocol outlines a multi-phase, evidence-based methodology for constructing a comprehensive cancer surveillance framework, drawing on validated approaches from recent research [79] [80].
Phase 1: Requirement Analysis and Data Element Identification
- Systematic Review: Conduct a literature review following PRISMA guidelines. Search major databases (e.g., PubMed, Embase, Scopus) using keywords related to "cancer surveillance," "indicators," and "standardization." Screen results to identify critical epidemiological indicators and data standardization practices [79] [80].
- Comparative System Evaluation: Perform a comparative analysis of existing international cancer surveillance systems (e.g., WHO's Global Cancer Observatory, EU's European Cancer Information System, SEER program). Document their data elements, visualization tools, and analytical capabilities to identify universal elements and best practices [79] [80].
- Checklist Validation: Consolidate findings into a standardized data checklist. Validate the content using the Content Validity Ratio and assess reliability using Cronbach's alpha through expert consultation with oncologists, epidemiologists, and public health specialists [79].
Phase 2: System Design and Architecture
- Data Modeling: Use Unified Modeling Language to develop data flow, use-case, and sequence diagrams. Define a relational database schema to organize cancer patient data, epidemiological indicators, and analytical results [79].
- Modular Development: Implement a modular system architecture. Employ Django for back-end services and Vue.js for front-end development to create a responsive web interface. Develop an Application Programming Interface for seamless data exchange [79].
- Advanced Analytics Integration: Incorporate modules for Geographic Information System (GIS)-based spatial analysis and predictive modeling to forecast cancer incidence trends over 5-, 10-, and 20-year horizons [79].
Phase 3: Usability and Performance Evaluation
- Heuristic Assessment: Evaluate the system using Nielsen’s Heuristic Assessment, engaging medical informatics specialists, pathologists, and health managers. Resolve identified usability issues to enhance functionality and user satisfaction [79].
- Data Quality Metrics: Adhere to national data quality standards, such as those from the National Program of Cancer Registries, which mandate ≤5% death certificate-only cases, ≤3% missing age/sex data, and ≥97% of records passing standardized computerized edits [81].
Protocol 2: Optimized Risk-Based Surveillance for Pathogen Early Detection
This protocol details a computational approach for designing risk-based surveillance for invasive pathogens, optimizing site selection to maximize early detection probability [8] [9].
Step 1: Spatially Explicit Model Development
- Landscape Parametrization: Create a gridded landscape (e.g., 1 km² cells) of the host population. Integrate data on host density from commercial and residential sources, such as census data [8] [9].
- Pathogen Introduction and Spread Simulation: Develop a stochastic, spatially explicit model. Simulate pathogen entry at high-risk sites and model secondary spread using an exponential dispersal kernel. Continue simulations until a predefined maximum acceptable prevalence threshold is exceeded. Run a large number of simulations to capture spatiotemporal variability.
Step 2: Surveillance Strategy Optimization
- Define Surveillance Parameters: Set logistical constraints, including the number of surveillance sites, sampling intensity (number of hosts assessed per site), sampling frequency, and the diagnostic sensitivity of the detection method [8].
- Stochastic Optimization: Use a computational optimization routine, such as simulated annealing, to identify the arrangement of surveillance sites that maximizes the probability of detecting the pathogen before it reaches the prevalence threshold across all simulation runs [8] [9].
- Strategy Comparison: Compare the performance (detection probability and cost) of the optimized surveillance strategy against conventional risk-based approaches that target only the highest-risk sites [8].
Step 3: Validation and Cost-Benefit Analysis
- Performance Metrics: Calculate the probability of detection and the time to detection for the optimized strategy versus conventional methods.
- Economic Evaluation: Quantify the cost savings achieved by the optimized strategy, considering reduced sampling and laboratory testing requirements while maintaining high detection sensitivity [8].
Data Presentation and Quantitative Standards
Table 1: Core Data Elements for a Standardized Cancer Surveillance Framework
Table 1: Essential data elements and standards for a comprehensive cancer surveillance system, synthesized from international frameworks [79] [82] [80].
| Data Category | Specific Elements | Measurement Standards | Purpose |
|---|---|---|---|
| Epidemiological Indicators | Incidence, Prevalence, Mortality, Survival Rates, Years Lived with Disability (YLD), Years of Life Lost (YLL) | Age-standardized using multiple standard populations (e.g., SEGI, WHO) | Assess burden and trends |
| Demographic Variables | Age, Sex, Race, Ethnicity, Geographic Location (County) | Stratified analysis filters | Identify disparities and high-risk groups |
| Tumor Characteristics | Primary Site, Morphology, Behavior, Stage at Diagnosis | ICD-O-3 standards; Cancer PathCHART recommendations | Case classification and prognosis |
| Data Source & Quality | Reporting Source (Hospital, Pathology, Death Certificate), Completeness, Timeliness | NPCR/SEER standards; ≤5% missing critical data | Ensure data validity and reliability |
Table 2: Key Attributes for Evaluating Surveillance System Performance
Table 2: Operational attributes and metrics for evaluating the usefulness and efficiency of public health surveillance systems, as defined by CDC guidelines [65].
| Attribute | Definition | Evaluation Measure |
|---|---|---|
| Simplicity | Ease of operation and structure | Staff time spent on maintenance, data collection, and analysis; number of reporting sources |
| Flexibility | Ability to adapt to changing needs | Ease of incorporating new health events, data sources, or technologies |
| Acceptability | Willingness to participate | Reporting completeness by data providers; participation rate |
| Sensitivity | Ability to detect health events | Proportion of actual cases identified by the system |
| Predictive Value Positive | Proportion of reported cases that are true cases | Number of false positives among reported cases |
| Representativeness | Accuracy in reflecting the population | Comparison of surveillance data demographics with population demographics |
| Timeliness | Speed between steps in surveillance | Time from diagnosis to report; from report to public health action |
Visualization of Framework Components
Workflow for Developing a Risk-Based Surveillance Framework
The following diagram illustrates the integrated, multi-phase workflow for developing and implementing a risk-based surveillance framework, applicable to both cancer and infectious diseases.
Logic of Risk-Based Surveillance Site Selection
This diagram contrasts the decision logic of conventional versus optimized risk-based surveillance strategies for early pathogen detection.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential tools, models, and reagents for developing and implementing advanced risk-based surveillance systems.
| Tool/Reagent | Type/Platform | Function in Surveillance Research |
|---|---|---|
| ICD-O-3 / Cancer PathCHART | Coding Standard | Provides gold-standard terminology and codes for tumor site, histology, and behavior, ensuring data consistency [83]. |
| Spatially Explicit Stochastic Model | Computational Model | Simulates pathogen introduction and spread through a real-world host landscape to inform surveillance design [8] [9]. |
| Simulated Annealing Algorithm | Optimization Routine | Identifies the optimal arrangement of surveillance sites to maximize detection probability within resource constraints [8]. |
| Django & Vue.js | Software Framework | Enables development of scalable, modular surveillance systems with robust back-end (Django) and responsive front-end (Vue.js) [79]. |
| GIS Integration Tools | Analytical Software | Facilitates spatial analysis, hotspot identification, and visualization of disease distribution and risk factors [79]. |
| Nielsen’s Heuristic Assessment | Evaluation Checklist | A structured method for usability testing of surveillance system interfaces by domain experts [79]. |
| CDC's EDITS Software | Data Quality Tool | Applies standardized computerized edits to validate the logic and consistency of cancer registry data [81]. |
Conclusion
Risk-based surveillance is an indispensable, evolving strategy that enhances early detection capabilities across the biomedical spectrum. The synthesis of insights from clinical development, public health, and regulatory science confirms that a proactive, prioritized approach is superior to traditional methods for protecting patient safety and public health. Future success hinges on global harmonization of regulations, increased integration of novel technologies and data analytics, and the adoption of comprehensive frameworks like One Health. For researchers and drug developers, embracing these advanced, validated strategies is paramount for accelerating the development of safe therapies and effectively preventing, detecting, and responding to emerging threats in an increasingly complex global landscape.
References
- 1. Hippocratic oath: Losing relevance in today's world? - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC6482690/]
- 2. Relevance of the Hippocratic Oath in the 21st Century [https://ascopost.com/issues/october-15-2014/relevance-of-the-hippocratic-oath-in-the-21st-century.aspx]
- 3. ICH E6(R3) Explained: A Guide to the 2025 GCP Update [https://intuitionlabs.ai/articles/ich-e6-r3-gcp-guidelines-2025]
- 4. The Impact of ICH E6(R3) on U.S. and Canadian IRBs [https://www.advarra.com/blog/the-impact-of-ich-e6r3-on-u-s-and-canadian-irbs/]
- 5. Modern Hippocratic Oath | UCLA Med School [https://medschool.ucla.edu/blog-post/modern-hippocratic-oath-holds-the-underlying-values-of]
- 6. Safety Surveillance During Drug Development [https://pmc.ncbi.nlm.nih.gov/articles/PMC10075498/]
- 7. What is Risk-Based Monitoring (RBM)? [https://www.transceleratebiopharmainc.com/rbminteractiveguide/what-is-risk-based-monitoring-rbm/introduction/]
- 8. Optimising risk-based surveillance for early detection of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7581011/]
- 9. Optimising risk-based surveillance for early detection of ... [https://journals.plos.org/plosbiology/article%3Fid%3D10.1371/journal.pbio.3000863]
- 10. Oversight of Clinical Investigations — A Risk-Based ... [https://www.fda.gov/regulatory-information/search-fda-guidance-documents/oversight-clinical-investigations-risk-based-approach-monitoring]
- 11. Risk Assessment Methodologies [https://www.cisa.gov/resources-tools/resources/risk-assessment-methodologies]
- 12. Why Effective Controls are Essential to Mitigate Risk [https://riskonnect.com/internal-audit/why-effective-controls-are-essential-to-mitigate-risk/]
- 13. Risk assessment: An overview [https://legal.thomsonreuters.com/blog/what-is-a-risk-assessment/]
- 14. Keys to Developing an Effective Risk Assessment ... [https://auditboard.com/blog/risk-assessment-methodology]
- 15. 6 Risk Assessment Methodologies Types and How to ... [https://www.metricstream.com/learn/risk-assessment-methodology.html]
- 16. What are controls in risk management? [https://www.dataguard.com/blog/what-are-controls-in-risk-management/]
- 17. 6 Key Questions to Define Risk Control - Updated 2025 [https://www.protechtgroup.com/en-us/blog/risk-management-controls]
- 18. Strategic Plan for Risk Communication [https://www.fda.gov/about-fda/reports/strategic-plan-risk-communication]
- 19. Risk Communication and the Pharmaceutical Industry [https://pubmed.ncbi.nlm.nih.gov/23061779/]
- 20. Drug Safety Communications [https://www.fda.gov/drugs/drug-safety-and-availability/drug-safety-communications]
- 21. Quantification of the sensitivity of early detection surveillance [https://pmc.ncbi.nlm.nih.gov/articles/PMC7267659/]
- 22. Risk-Based Monitoring in Clinical Trials: 2021 Update - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9829217/]
- 23. The Evolution of Risk-Based Approaches in Clinical Trials [https://www.eclinicalsol.com/blog/the-evolution-of-risk-based-approaches-in-clinical-trials/]
- 24. Optimizing surveillance for early disease detection: Expert ... [https://www.sciencedirect.com/science/article/abs/pii/S016758772100163X]
- 25. Designing and evaluating risk-based surveillance systems [https://www.sciencedirect.com/science/article/abs/pii/S0167587711004004]
- 26. Concepts for risk-based surveillance in the field of ... [https://pubmed.ncbi.nlm.nih.gov/16507106/]
- 27. Track changes in International Regulations: Global Trade ... [https://www.xnovainternational.com/post/track-changes-in-international-regulations-global-trade-2025]
- 28. How are firms tackling fragmented global regulations? [https://fintech.global/cx-fintech-forum/2025/08/01/how-are-firms-tackling-fragmented-global-regulations/]
- 29. Risk based surveillance for early detection of low ... [https://www.sciencedirect.com/science/article/pii/S0167587714002670]
- 30. 10 Steps to Implement RBQM for Your Clinical Trial [https://cluepoints.com/10-steps-for-practical-rbqm-implementation-for-your-business/]
- 31. International Council for Harmonisation E ( 6 ) addendum: Challenges... R 2 [https://pmc.ncbi.nlm.nih.gov/articles/PMC5654214/]
- 32. Evaluation of risk-based antigen and antibody surveillance ... [https://pubmed.ncbi.nlm.nih.gov/40678492/]
- 33. Personalized Risk-Adaptive Surveillance Strategies in Cancer ... [https://sop.washington.edu/choice/research/research-projects/personalized-risk-adaptive-surveillance-strategies-in-cancer/]
- 34. Risk-Based Quality Management in Clinical Data ... [https://www.quanticate.com/blog/risk-based-quality-management-in-clinical-data-management]
- 35. Comprehensive Assessment of Risk-Based Quality ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11043178/]
- 36. Toolkit for ICH ( E ) 6 for Small to... R 2 Quality Risk Management [https://link.springer.com/article/10.1007/s43441-019-00004-6]
- 37. A visual safety risk evaluation tool in early clinical phases [https://www.sciencedirect.com/science/article/pii/S1551714425001478]
- 38. A visual safety risk evaluation tool in early clinical phases [https://pubmed.ncbi.nlm.nih.gov/40381907/]
- 39. A Guide to Understanding 5x5 Risk Assessment Matrix [https://safetyculture.com/topics/risk-assessment/5x5-risk-matrix]
- 40. Risk Assessment Matrix: Overview and Guide [https://auditboard.com/blog/what-is-a-risk-assessment-matrix]
- 41. Colors Of Safety: Your Guide To Color Codes And Meanings [https://www.safetydecals.com/blogs/news/colors-of-safety?srsltid=AfmBOorrT5Gn-lg-0kme65aRgeAcTeVkM0_UCXBnqfhoVTGHB5WcTa6F]
- 42. How To Prevent Your AV Project From Catching Fire ... [https://chroma.fm/news/project-risk-how-to-prevent-your-av-project-from-catching-fire]
- 43. Application of an innovative grid-based surveillance strategy ... [https://bmcpublichealth.biomedcentral.com/articles/10.1186/s12889-022-13753-1]
- 44. Beyond Certification: How China Keeps Malaria at Bay [https://apmen.org/blog/beyond-certification-how-china-keeps-malaria-bay]
- 45. Centralized Monitoring: A 360° Approach to Clinical ... [https://www.medidata.com/en/life-science-resources/medidata-blog/centralized-monitoring/]
- 46. What Real-Time Data Analytics Really Means and Why It's So ... [https://www.sigmacomputing.com/blog/what-real-time-data-analytics-really-means-and-why-its-so-important]
- 47. Improving risk stratification and detection of early HCC ... [https://www.sciencedirect.com/science/article/pii/S2589555925001880]
- 48. Resource-Poor Settings: Infrastructure and Capacity Building [https://pmc.ncbi.nlm.nih.gov/articles/PMC6679686/]
- 49. Inequality in infrastructure access and its association with ... [https://www.nature.com/articles/s41562-025-02208-3]
- 50. Surveillance strategy for early detection of unusual infectious ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7102709/]
- 51. 'A tough nut to crack': inconsistent standards as roadblocks ... [https://pubmed.ncbi.nlm.nih.gov/40692612/]
- 52. Health Data Interoperability & Integration in 2025 [https://talencio.com/breaking-barriers-health-data-interoperability-integration-in-2025/]
- 53. Data Standards Fatigue? [https://globalforum.diaglobal.org/issue/february-2025/data-standards-fatigue/]
- 54. Interoperability in 2025 - What You Need to Know [https://www.nextech.com/blog/interoperability-healthcare]
- 55. 2025 Trends: Advancements in Data Interoperability [https://www.appliedclinicaltrialsonline.com/view/2025-trends-advancements-data-interoperability]
- 56. Quantitatively assessing early detection strategies for ... [https://www.nature.com/articles/s41467-023-44199-7]
- 57. Global Antimicrobial Resistance and Use Surveillance ... [https://www.who.int/initiatives/glass]
- 58. Towards a Harmonized Segmentation Protocol - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4387011/]
- 59. The World Health Organization STEPwise Approach to ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4695948/]
- 60. Weekly US Influenza Surveillance Report: Key Updates for ... [https://www.cdc.gov/fluview/surveillance/2025-week-45.html]
- 61. Strengthening disease surveillance capacity at national ... [https://www.sciencedirect.com/science/article/pii/S0033350624001872]
- 62. Harnessing technology for infectious disease response in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11245197/]
- 63. Breaking Down Silos: How to Foster Cross-Functional ... [https://fullscale.io/blog/cross-functional-collaboration-development-product-design/]
- 64. 9 Steps to Building Cross-Functional Teams That Drive ... [https://www.edstellar.com/blog/how-to-build-cross-functional-team]
- 65. Guidelines for Evaluating Surveillance Systems [https://www.cdc.gov/mmwr/preview/mmwrhtml/00001769.htm]
- 66. Concepts for risk - based in the field of veterinary... surveillance [https://bmchealthservres.biomedcentral.com/articles/10.1186/1472-6963-6-20]
- 67. Comparative Performance Evaluation of the Public Health ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10131602/]
- 68. Comparison of surveillance-based metrics for the assessment ... [https://bmcmedresmethodol.biomedcentral.com/articles/10.1186/s12874-017-0328-2]
- 69. A Framework for Evaluating the Use of Surveillance ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12307093/]
- 70. Enabling quantitative comparison of wastewater ... [https://www.sciencedirect.com/science/article/abs/pii/S0048969724062296]
- 71. Postmarketing Surveillance Programs [https://www.fda.gov/drugs/surveillance/postmarketing-surveillance-programs]
- 72. Developing a quality and safety surveillance system [https://pmc.ncbi.nlm.nih.gov/articles/PMC12121783/]
- 73. Qualitative vs. Quantitative Cybersecurity Risk Assessment [https://securityscorecard.com/blog/qualitative-vs-quantitative-risk-assessment/]
- 74. Quantitative Risk Management vs. Qualitative Risk Analysis [https://riskonnect.com/operational-resilience/quantitative-risk-management-vs-qualitative-risk-analysis/]
- 75. 2021 Volume 2 Risk Assessment and Analysis Methods [https://www.isaca.org/resources/isaca-journal/issues/2021/volume-2/risk-assessment-and-analysis-methods]
- 76. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 77. Risk Based Monitoring Toolbox | Ecrin [https://ecrin.org/risk-based-monitoring-toolbox]
- 78. NIMH Guidance on Risk-Based Monitoring [https://www.nimh.nih.gov/funding/clinical-research/nimh-guidance-on-risk-based-monitoring]
- 79. Design, development, and evaluation of an advanced cancer ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12487559/]
- 80. A systematic review and comparative evaluation to develop ... [https://archpublichealth.biomedcentral.com/articles/10.1186/s13690-025-01584-6]
- 81. NPCR Standards [https://www.cdc.gov/national-program-cancer-registries/about/npcr-standards.html]
- 82. Cancer Surveillance Programs and Data Tracking [https://www.cancer.org/cancer/preparing-for-treatment/cancer-surveillance-programs-and-data-tracking.html]
- 83. Cancer PathCHART - Tumor Site-Morphology Surveillance ... [https://seer.cancer.gov/cancerpathchart/]